VulnWatch Monday: CVE-2026-3611 🔓
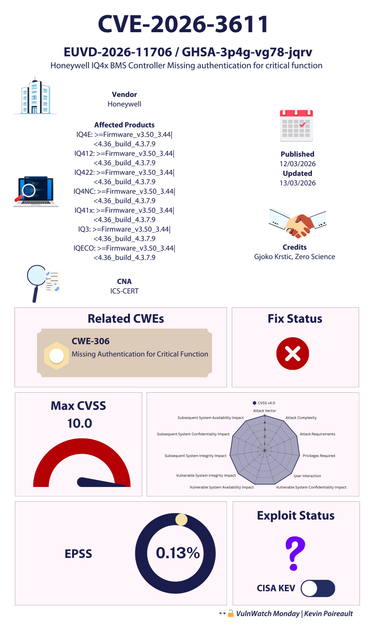
Gjoko Krstic, from Zero Science Lab reported a maximum-severity vulnerability in Honeywell's IQ4x building management controller.
The flaw was publicly disclosed by ICS Cert and is tracked as CVE-2026-3611.
🔎 With no user module configured, security is disabled by design and the system operates under a System Guest (level 100) context, granting read/write privileges to any party able to reach the HTTP interface.
⚙️ Authentication controls are only enforced after a web user is created via U.htm, which dynamically enables the user module. Because this function is accessible prior to authentication, a remote user can create a new account with administrative read/write permissions enabling the user module and imposing authentication under attacker-controlled credentials. This action can effectively lock legitimate operators out of local and web-based configuration and administration.
🔧 According to CISA, Honeywell is aware of the issue, but has not released a fix. For more information, users are urged to contact Honeywell directly.
⚠️ CISA advisory: https://www.cisa.gov/news-events/ics-advisories/icsa-26-069-03
💾 View CSAF: https://github.com/cisagov/CSAF/blob/develop/csaf_files/OT/white/2026/icsa-26-069-03.json