Tiens, jolie démo et trouvaille!
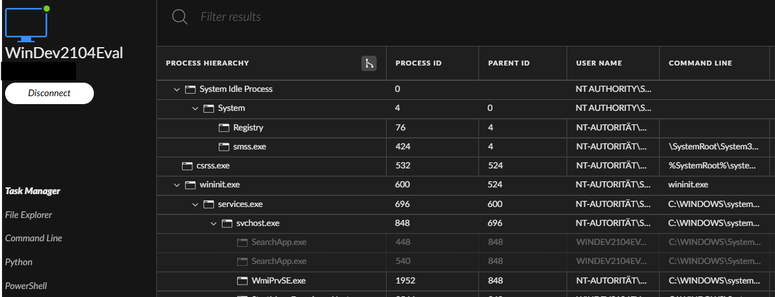
l'équipe redteam d' Infoguard 🫕 a décortiqué le système de communication pour la prise de contrôle à distance de l'EDR de Palo Cortex pour la détourner en mode Living-off-the-Land
👇
https://labs.infoguard.ch/posts/abusing_cortex_xdr_live_response_as_c2/
.
.
.
.
The only hurdle is that Cortex has default rules to block and detect when its own processes are started by a non-standard parent process
Bypasses for these rules will not be published in this post. 😈 😢
 decio
decio