𝐂𝐫𝐢𝐭𝐢𝐜𝐚𝐥 𝐙𝐞𝐫𝐨-𝐂𝐥𝐢𝐜𝐤 𝐅𝐥𝐚𝐰 𝐢𝐧 𝐧𝟖𝐧 𝐀𝐥𝐥𝐨𝐰𝐬 𝐅𝐮𝐥𝐥 𝐒𝐞𝐫𝐯𝐞𝐫 𝐂𝐨𝐦𝐩𝐫𝐨𝐦𝐢𝐬𝐞
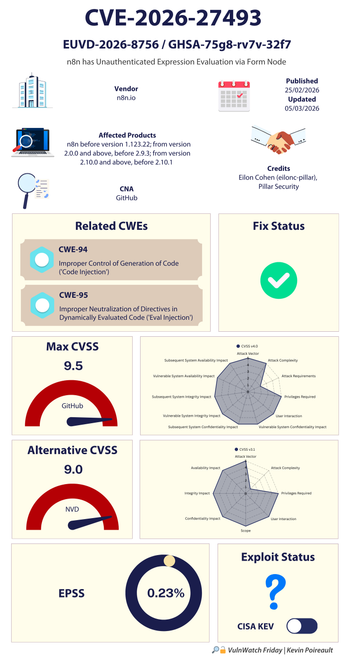
Researchers from Pillar Security have found two new critical vulnerabilities in self-hosted and cloud n8n deployments.
n8n is a popular open-source workflow automation platform powering hundreds of thousands of enterprise AI systems worldwide.
One of the flaws, tracked as CVE-2026-27493, can lead to full takeover of a server without the target clicking on anything and without the attacker needing to be authenticated.
🔧Fix? n8n cloud users should have already benefitted from automated fixes.
People self-hosting n8n instances are urged to update to versions 2.10.1, 2.9.3 or 1.123.22 of n8n, depending on their release channel.
Pillar Security also recommended users to rotate all stored credentials if a vulnerable workflow is found in their n8n environment.
https://www.infosecurity-magazine.com/news/critical-zeroclick-flaw-n8n-pillar/