@ktims
It's not modifying the field name. It's modifying the field value (adding a space). The name being lowercased is fine (that's just an HTTP/2 thing AIUI).
The ActivityPub spec is here:
https://swicg.github.io/activitypub-http-signature/
And it references:
https://datatracker.ietf.org/doc/html/draft-cavage-http-signatures-12
And that explicitly calls out proxies, but does not call out any specific headers that are problematic.
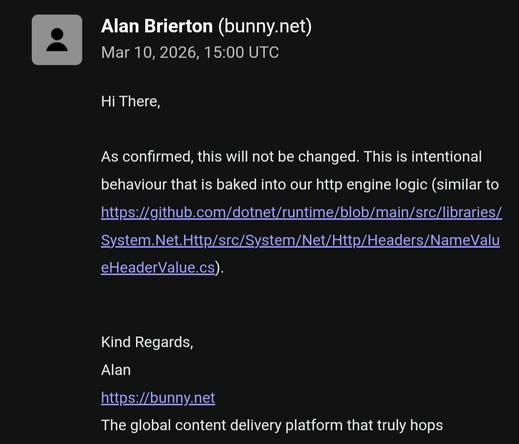
Unfortunately, since the servers that do the signing are the remote servers, this is not going to be fixed across the ecosystem any time soon. So regardless of who is "wrong" here, the status quo is Bunny is not usable for this purpose.
Ordering is already normalized and only a subset of headers are signed. The problem here is a header value is being modified.