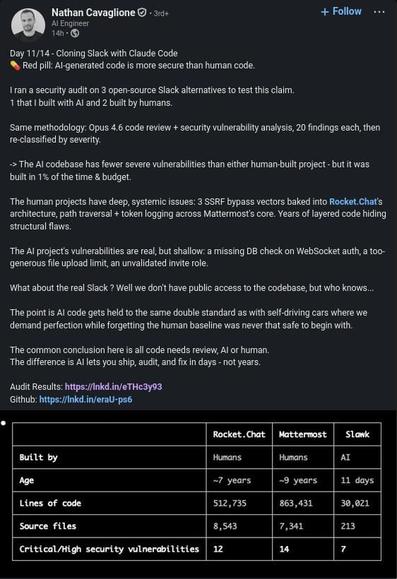
I saw this post on my feed, and caught my eye because I self-host a Mattermost instance. The fact that it has possible critical security issues is a concern for me. So I checked the github issue with the details: https://github.com/ncvgl/slawk/issues/107
Of course, it's fully LLM generated, but that's to be expected. So I opened the first issue described there, a *CRITICAL VULNERABILITY*, a possibility for XSS in email templates. Ok, sure, let's dig deeper.