Ah yep
#realworldcrypto
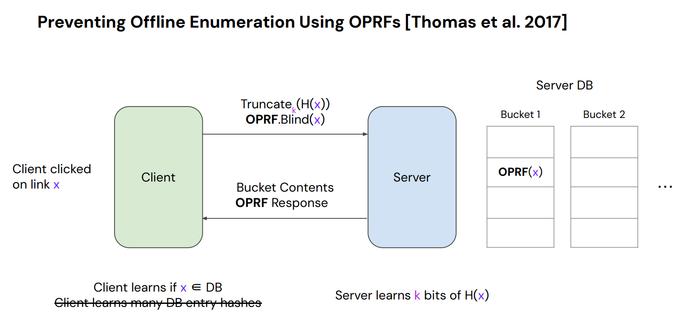
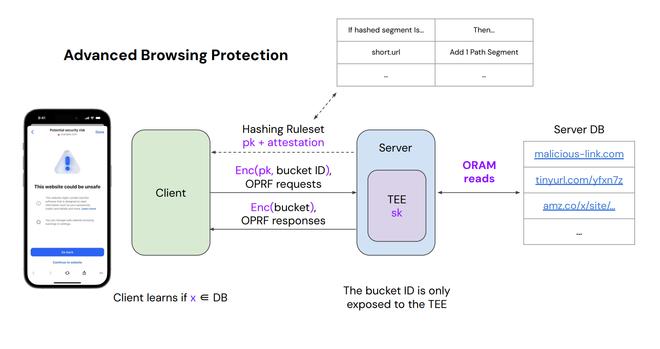
Want to protect against offline enumeration attacks
#realworldcrypto
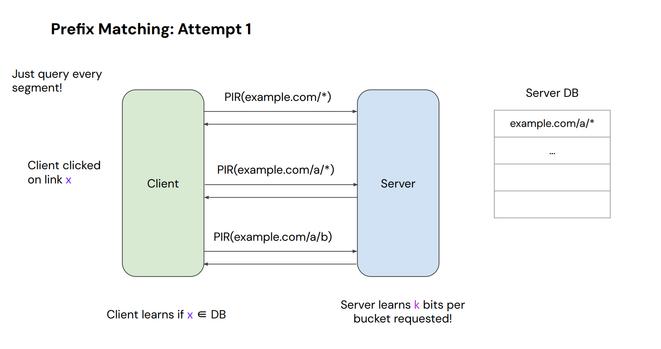
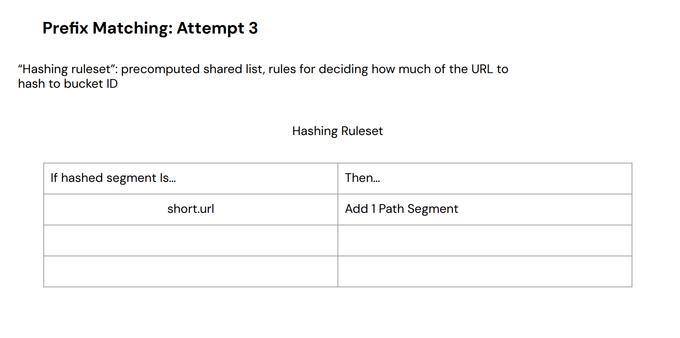
Prefix matching support; multiple attempts
#realworldcrypto
'attempts were made'
#realworldcrypto
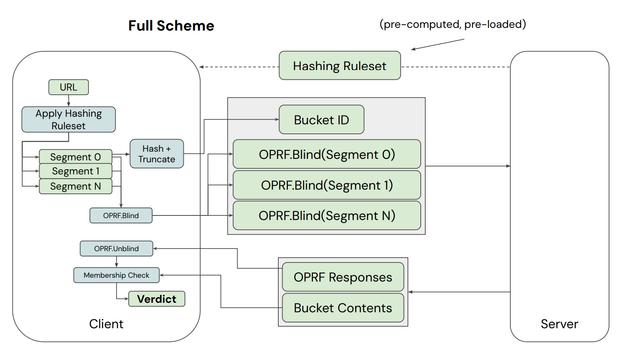
Full scheme (🥵)
#realworldcrypto
Oh boy
#realworldcrypto
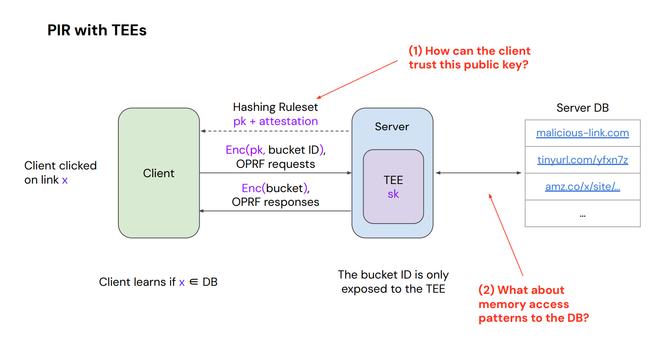
How do we retrieve things from the server, and how can we trust that the machine is actually doing what we expect it to do? Answer: attestation
#realworldcrypto
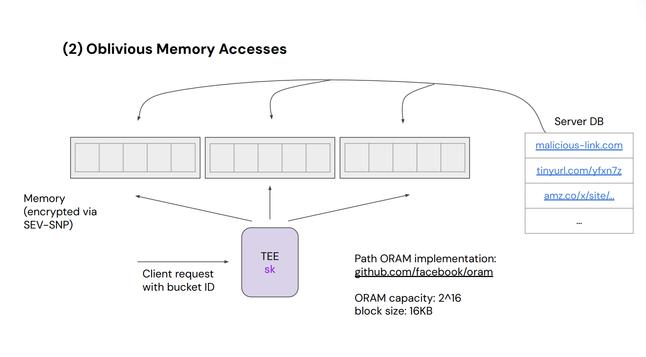
Want to avoid leaking these memory access patterns
#realworldcrypto
Future work: further reducing reliance on hardware assumptions, improve efficiency of ORAM use
#realworldcrypto
Next up, 'Improving the Trustworthiness of Javascript on the Web', presented by Michael Rosenberg, Giulio Berra, Ezzudin Alkotob, and Dennis Jackson
#realworldcrypto
should out @[email protected]
#realworldcrypto
[uh i don't necessarily agree this is why we trust iOS Signal vs say a web page as it exists]
#realworldcrypto
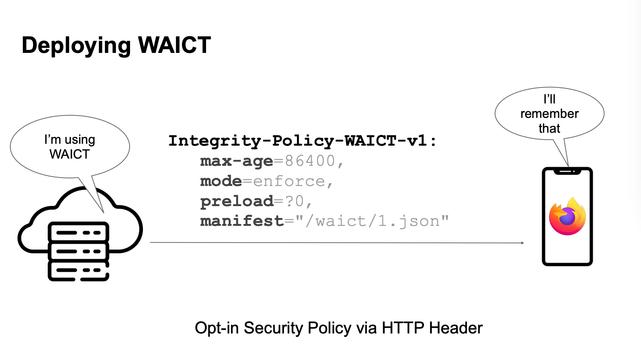
WAICT [is not whack??]
#realworldcrypto
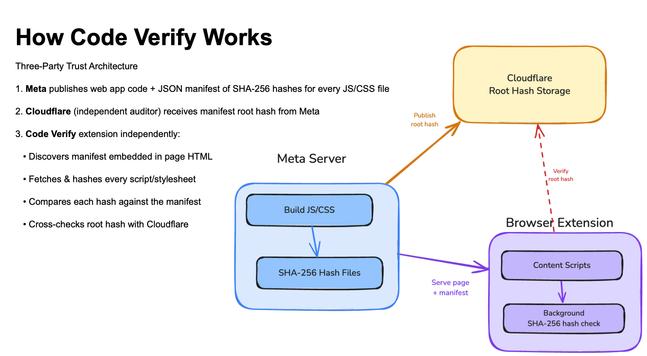
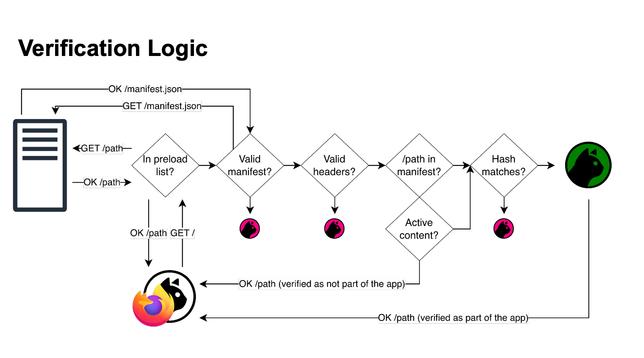
Code Verify: content, manifest, hash, store in public transparency log
#realworldcrypto
Code Verify is a browser extension that checks the log
#realworldcrypto
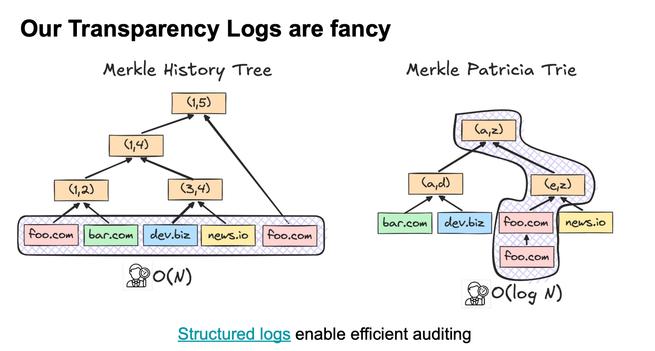
Each leaf of the manifest merkle tree is hash of one js or css file
#realworldcrypto
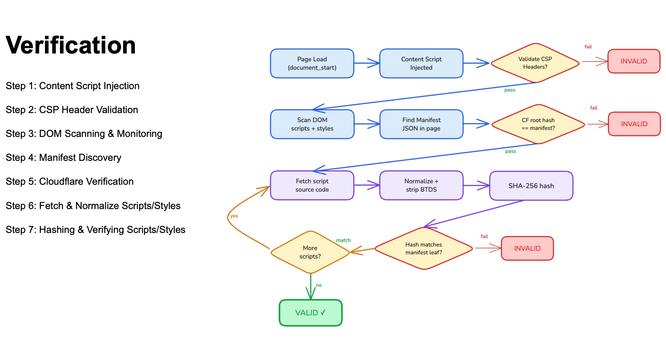
Web documents are complicated 😅
#realworldcrypto
WebCat
#realworldcrypto
WAICT— embedding into the browser
#realworldcrypto
Merkle Patricia Trees instead of traditional Merkle history trees, more efficient auditing
#realworldcrypto
Need immediate recovery through transparent opt-out
#realworldcrypto
prototype code working in firefox!
#realworldcrypto
Next up, 'Signal Lost (Integrity): The Signal App is More than the Sum of its Protocols', presented by Noemi Terzo and Kien Tuong Truong
#realworldcrypto
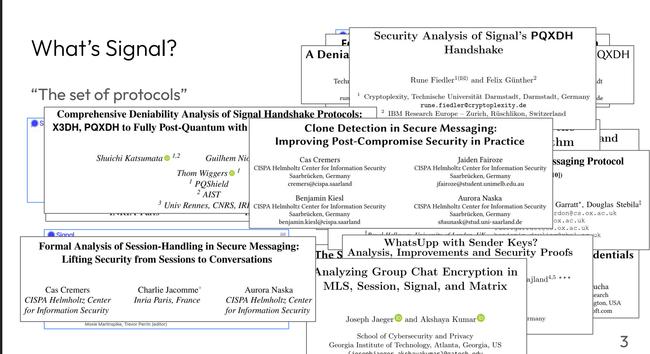
'Signal' is definitely more than just 'The Signal Protocol'
#realworldcrypto
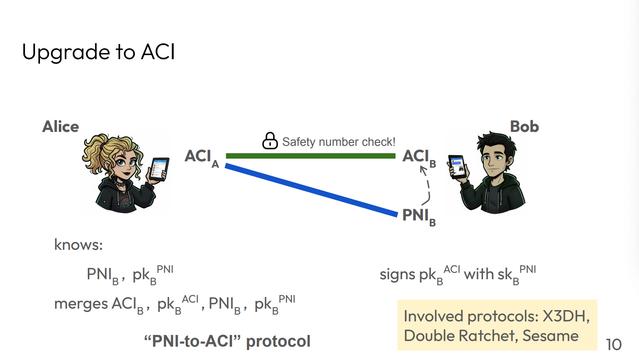
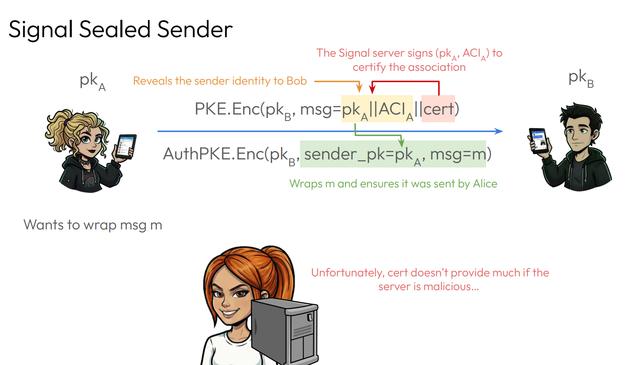
ACI: account identifier, PNI: phone number identifier
#realworldcrypto
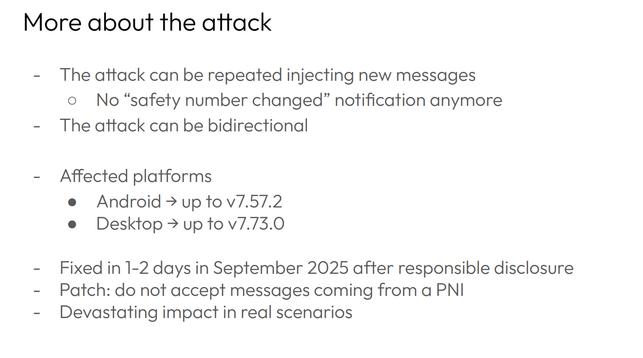
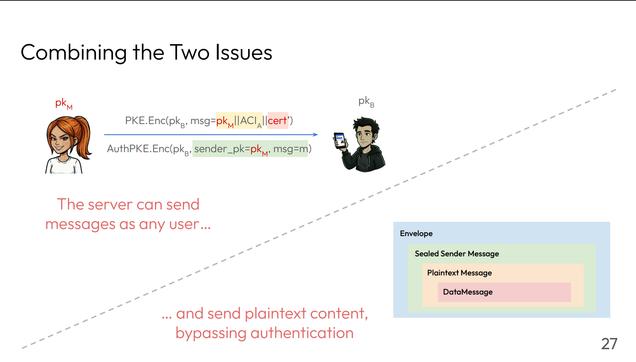
Affects the desktop and android clients, patched and fixed
#realworldcrypto
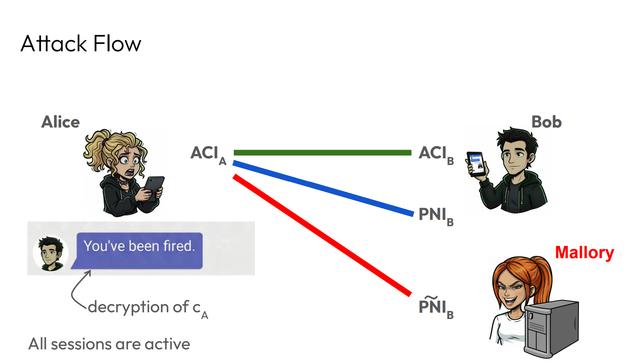
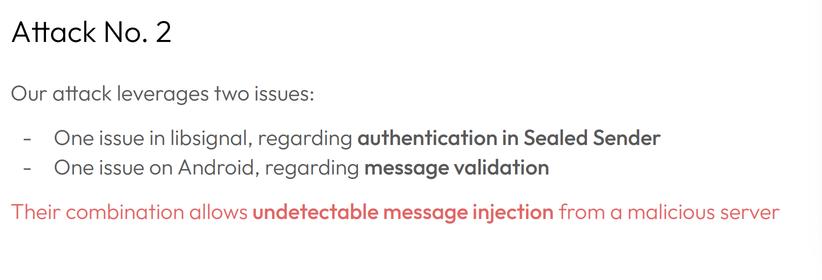
Leverages Sealed Sender
#realworldcrypto
The server can send Sealed Sender messages on behalf of anyone without detection (but the system is supposed to be secure in the setting that the server is insecure!)
#realworldcrypto
Existing Sealed Sender doesn't authenticate messages 😭
#realworldcrypto
How did we get here?
#realworldcrypto
'Boring' stuff matters: open source, documentation!!!, communication with community
#realworldcrypto
Ensure that cryptographic logic is _unified_ in a single native library [Is this possible in practice? Sounds less performant]
#realworldcrypto
Break time!
#realworldcrypto
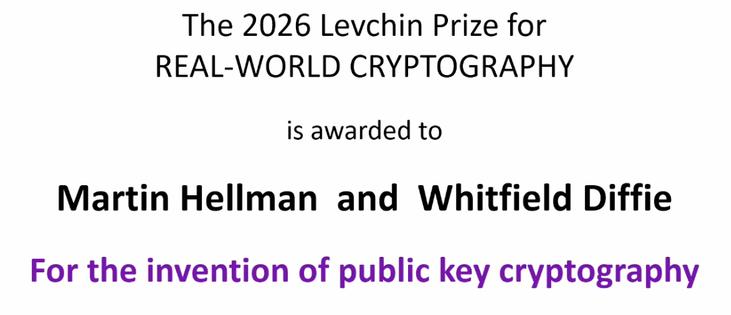
Next up, the Levchin Prize!
#realworldcrypto
The first set of winners: Diffie and Hellman!
#realworldcrypto
This is The Paper:
ee.stanford.edu/~hellman/pub...
#realworldcrypto
ee.stanford.edu/~hellman/publi...
ee.stanford.edu/~hellman/publi...
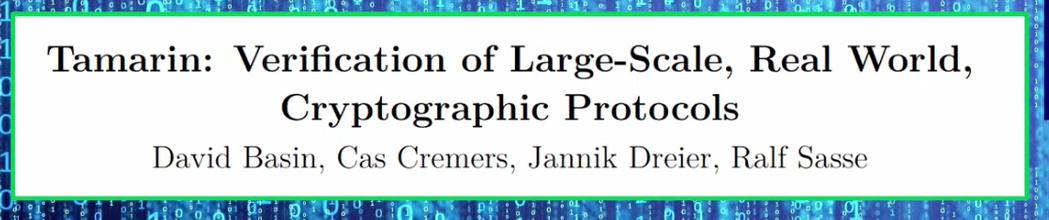
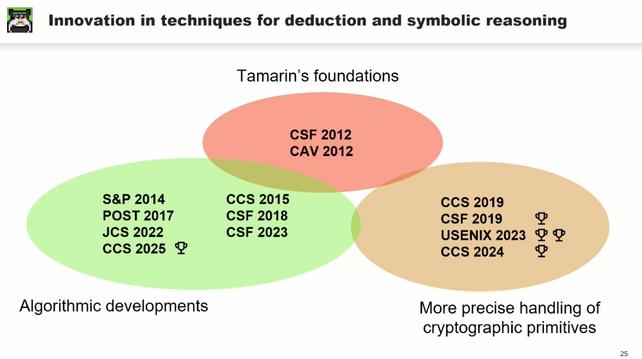
The second set of winners are the Tamarin prover team!!
#realworldcrypto
@cascremers.bsky.social gracefully accepts
#realworldcrypto
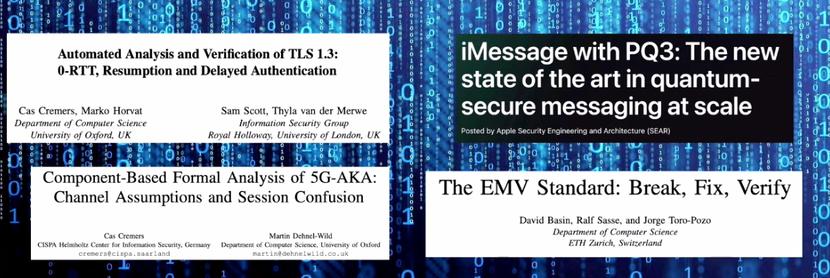
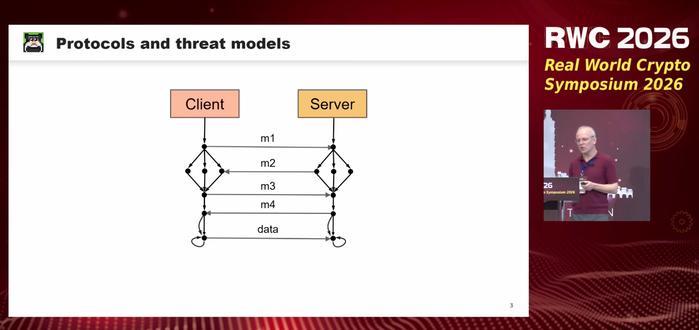
@cascremers.bsky.social gives the Levchin Prize invited talk on Tamarin
#realworldcrypto
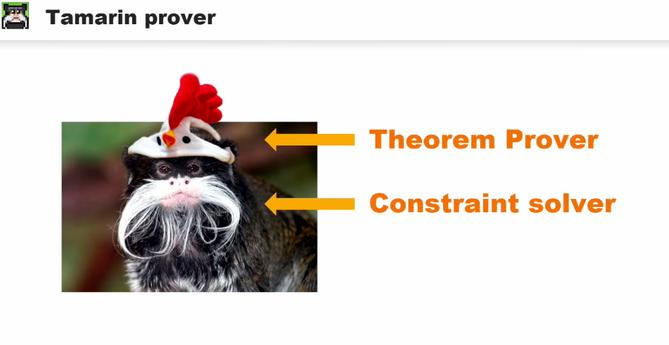
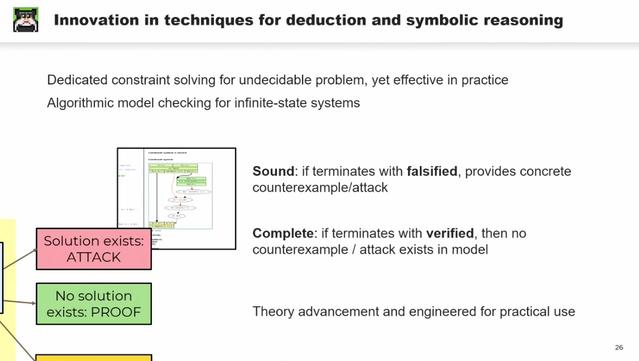
Tamarin is a constraint solver impersonating a theorem prover
#realworldcrypto
Ooo
#realworldcrypto
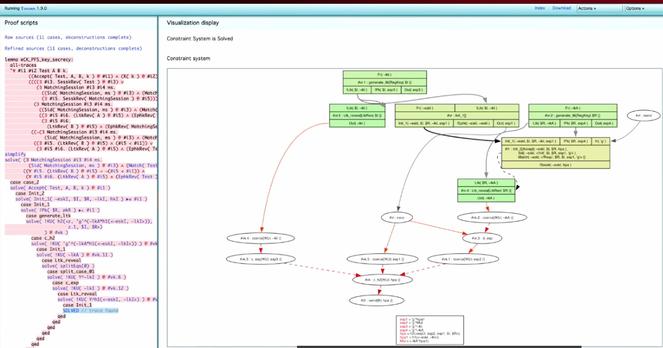
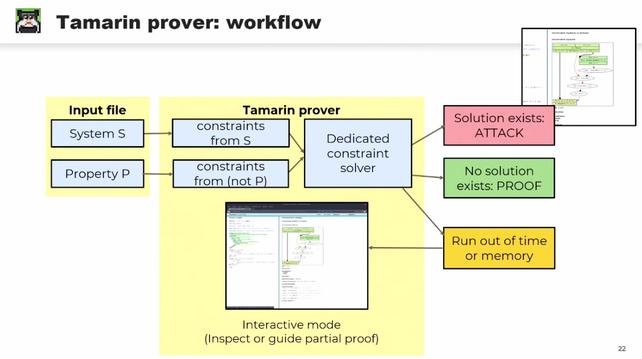
Undecidable problem— we can't be sure it will ever terminate
#realworldcrypto
Much more precise handling of cryptographic primitives, including those that are motivated by the symbolic modeling of protocols
#realworldcrypto
If Tamarin terminates, there is always either an attack or a proof of security (if it doesn't terminate, oop)
#realworldcrypto
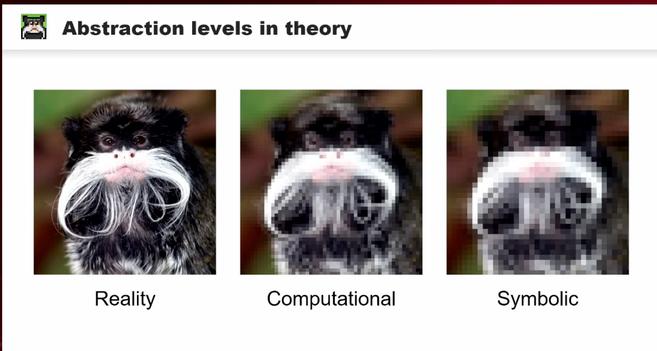
✨layers of abstraction✨
#realworldcrypto
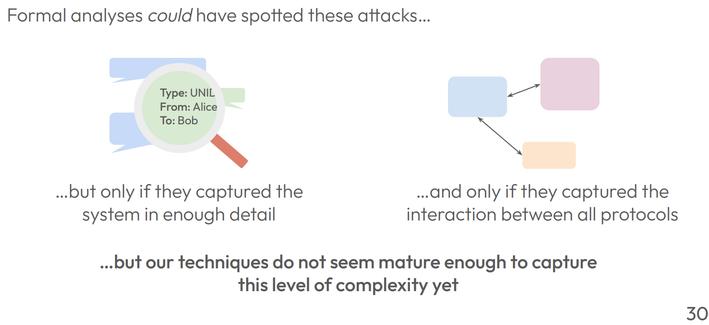
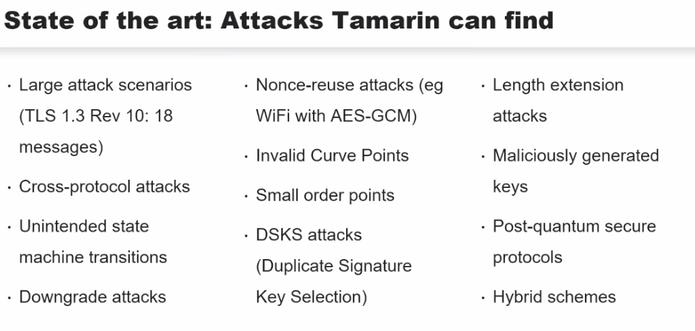
Can find complex attacks that humans will probably never find on their own
#realworldcrypto
Find attacks not by programming in the attacks, but by modeling the protocol, the security notions, the state transitions, and seeing what shakes out
#realworldcrypto
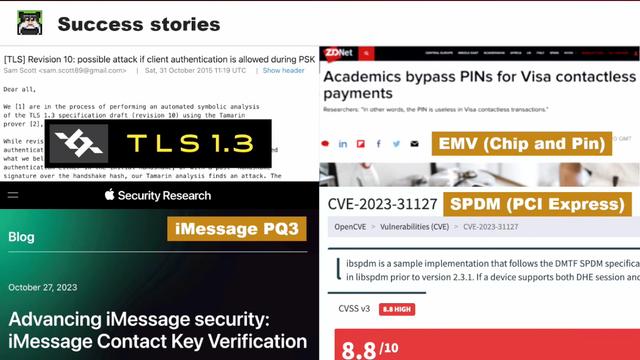
Many success stories of real world protocols
#realworldcrypto
New version of Tamarin out, and there's a new book!
#realworldcrypto
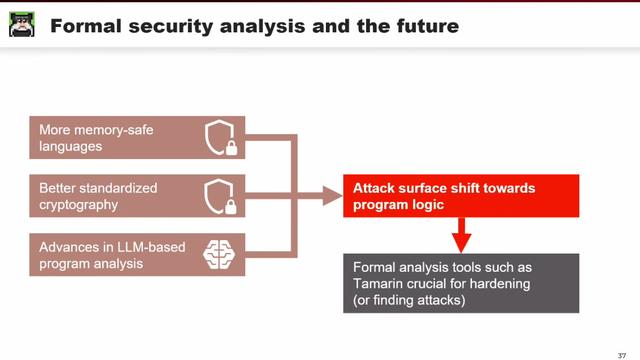
Future predictions:
#realworldcrypto