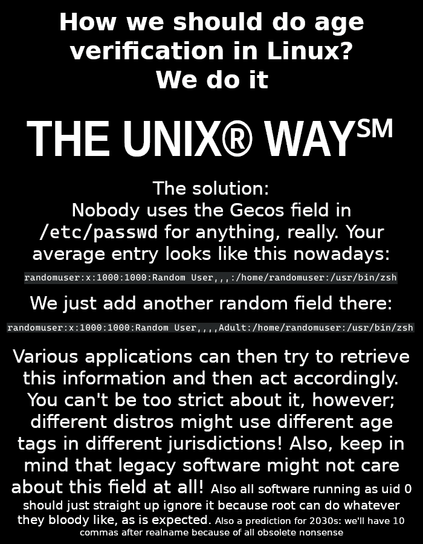
We can just do the adult check thing the usual way.
Age verification is just paving way for things a lot worse: globally unique identification.
They ( politicians ) will weaponize the inefficiencies in this implementation to push for an online verification later on.
And of course Peter Thiel will be somewhere in the middle
The problem with that whole situation is the way the law is written the developer is the one held responsible if a child circumvents the check to access adult content. Therefore, developers will have to pay hefty fines unless they:
-1: Have a way to positively make sure the person enters their age is telling the truth; and
-2: Lock this value from being changed by the user afterwards.
One can see how incredibly problematic this is for both privacy and true ownership and control over your own machine. There is also a lot that needs to be figured out in the law such as what will happen when someone inevitably finds a way to hack the system to circumvent it. Ultimately, big tech won’t care as much about the fines because of their deep pockets but small nonprofit open source projects will be killed.
This law is specifically designed to kill nonprofit-run and private software like Linux.
I do not know if that is true. Most of the political hacks writing these bills have zero understanding of computers and do not even consider Linux in the equation. They see Windows, iOS, Android and macOS.
This is more aimed at mom and dad with three children who have tablets for all the shits and take no responsibility for what the kids do with the devices.
Linux devs will just step back from releasing code packaged with installers and users will have to compile and set any given program up themselves.
I use MacPorts and Homebrew for what I need.
Most of the political hacks writing these bills have zero understanding of computers and do not even consider Linux in the equation.
Meta literally broke the record for the most legal bribery in a year over shifting the liability from platform to app store (as they’re facing tens of billions in fines). Apple and Google have been pumping tens of millions to counter it.
The political hacks are just reading what the corpos wrote for them…
I’ve started to believe that in fact, the political hacks do know what is going on with tech. They just do this shit anyway… Because they are sick at heart.
I feel like it is too late. People still do not care and will never care… We’ve lost.

28c3: The coming war on general computation
But think of all the pedophiles it will stop! Surely you don’t want pedophiles to get away with their crimes*? What are you, a pedophile?
- T&C apply, if you are a +1B shareholder, please disregard
+1B shareholder
Yep, because we all know the last people who would be pedophiles are billionaires.
(/s obviously)
That’s all it shares for now (for the California law). Once that’s in, what’s one more step, where the user has to provide proof of age, rather than just presenting one? That requires identification.
If their goal is identification, rather than actually protecting pedophiles (we know this isn’t the case because the Epstein clients are not facing consequences), then it’s easy to see how this leads to that.
The slippery slope is not always fallacious. If it’s a reasonable case, it’s just called a slippery slope argument.
Fingerprinting. Age, as well as factors like IP address, can be one more data point to individually identify a user with a certain number of accounts.
There’s also potential they changeover from “Enter your DOB” to “Show your driver’s license”, which they can collect much more data from.
I recently read an article from the creaters of PopOS. In that they raise a vaild point. If a child installs a virtualization software (say with the concent of an adult for educational purposes), then they can but browse internet through the VM, with them being the root user, pretending to be adults. It defeats the whole purpose of such verification methods. So their plan would to stick with ID based ones.
I think this was never about age verification, but to uniquely fingerprint every person using internet and to keep accountability.
Lets face it, the internet you knew is dead.
Lets face it, the internet you knew is dead.
Friendship ended with IP. Now I2P is friend.
I’ll just do what I’m always done since I was 10
“How old are you?”
“115 years young of course”
These laws are not written by the technically literate. They are written by attorneys based on the whims of old legislators who think that Siri is a real woman that they are talking to.
While the people who write the laws are competent, the legislators are not.
At the state level, it’s even worse because they are often given legislation carefully written by lobbyists and special interest groups.
If you have any inkling to run for office, please consider doing so because we need smarter people in every branch of government.
I guess, but also there are a ton more accurate fingerprinting methods other than dividing everyone up into buckets of <13, 13-15, 16-18, 18+. The vast majority of us are going to be 18+, so it’s a pretty weak signal.
Don’t get me wrong, the whole bill is absolutely riddled with issues and it’s extremely stupid, but this hardly provides significant data.
I think your monitor configuration (number of monitors and resolutions), video card, and installed fonts are going to go a LOT further than a bucket of 4 choices lol
Yes! Go get it. Exactly what needs to happen.
Hoping for the day one of the elites pushes a button, launches a nuclear, WW3 entails, and we all fucking perish. Its clear the world’s gonna end, might as well save all the trouble and end it now!!!
Pass.
Its my computer, I own it, gtfo and let me use it how ever I want.