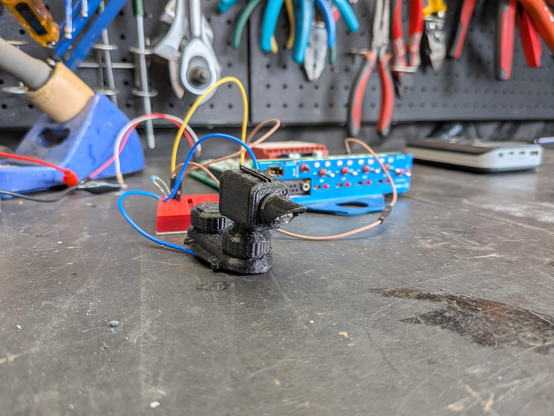
I got all my ducks in a row (ok, ignore the state of the kitchen right now)... but the blog post ones of you have been waiting for - Strobecom traffic light control details!
Also a little video of it working in practice.
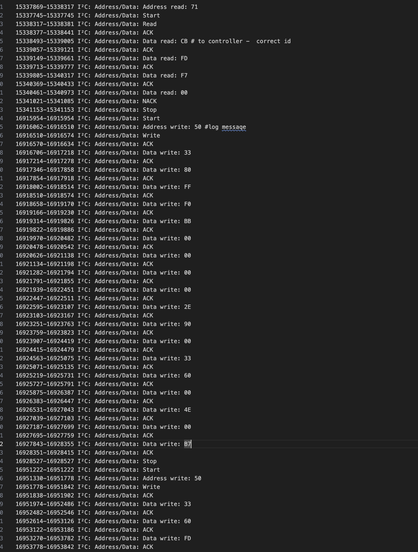
https://sprocketfox.io/xssfox/2026/03/04/strobecom-ii-reverse-engineering_-can-a-flipper-ze/