RE: https://mastodon.social/@pfandrade/116035886020550720
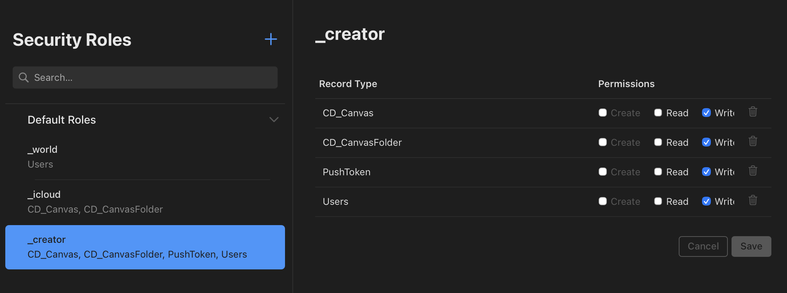
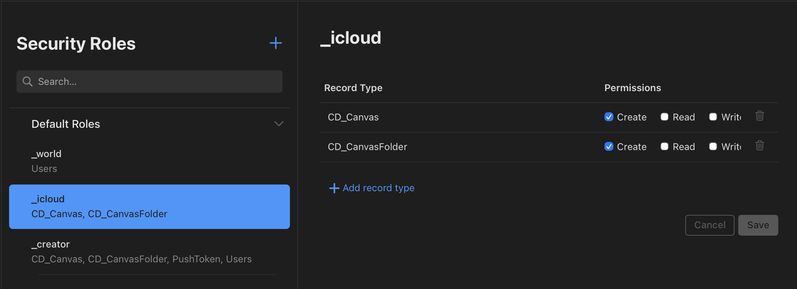
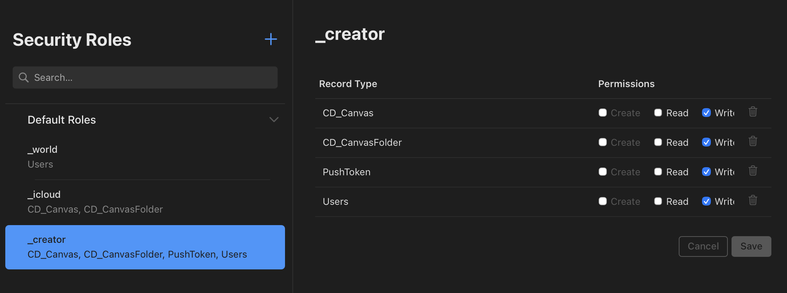
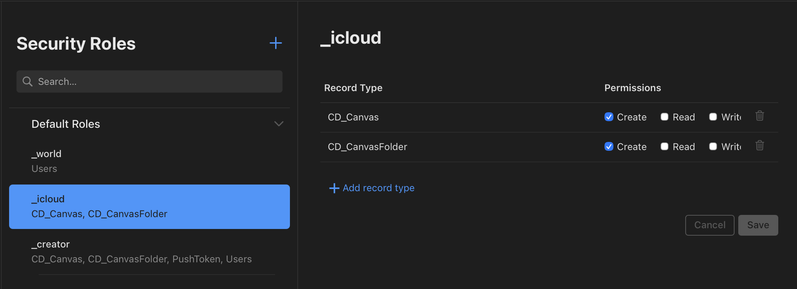
So can we actually use CloudKit's public database to store user-specific and/or sensitive data without it being widely available? So it's more like a traditional database an app can build functionality on?
Can anyone confirm this?
If that's the case, I've totally misunderstood the public database for years. I have always considered it suitable only for sample data and other data meant to be broadly accessible without auth.