#100DaysofYara - day 13
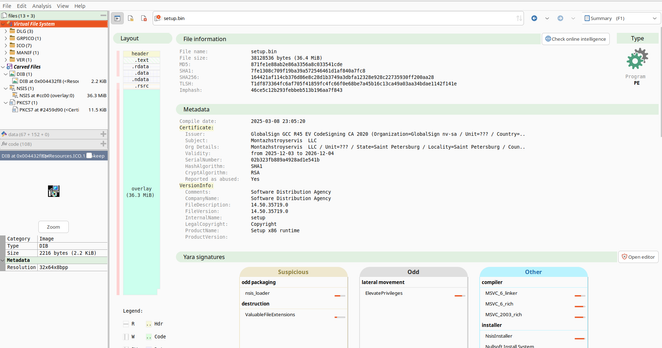
Came across a low detection malware which seems YARA resistant. Currently in use by ransomware actor.
I'll post some thoughts, but would love suggestions from others.
I'll explain the malware and show the best I could come up with.
Rule at bottom
1/7