🧵 Short Authentication Strings (SAS) in the Age of Generative AI
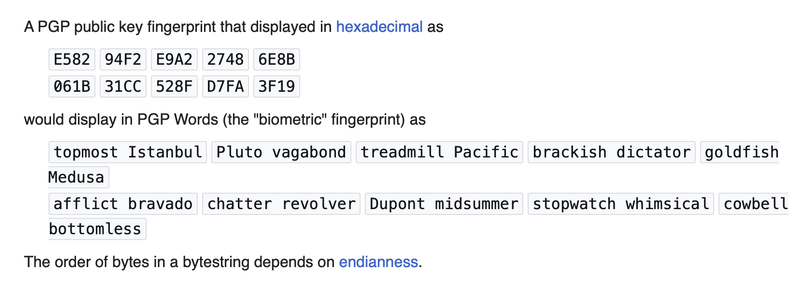
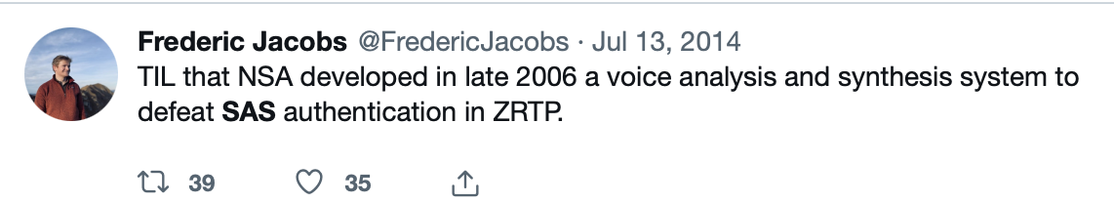
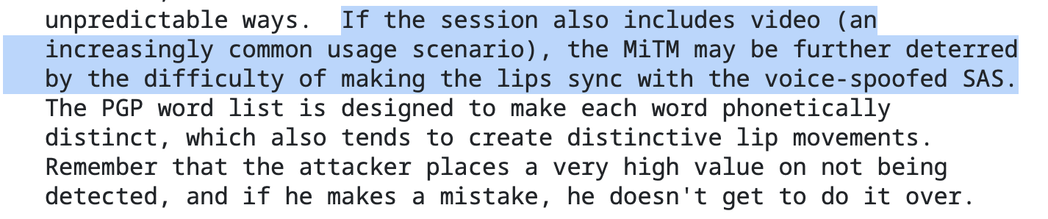
When ZRTP was released by Phil Zimmermann and team in the mid-2000s, one of it's main innovations was to use SAS in order to verbally authenticate the other party on the call and rule out person-in-the-middle attacks. This worked by reading aloud a SAS value over the voice connection and ensure that it matched the value on the other side.
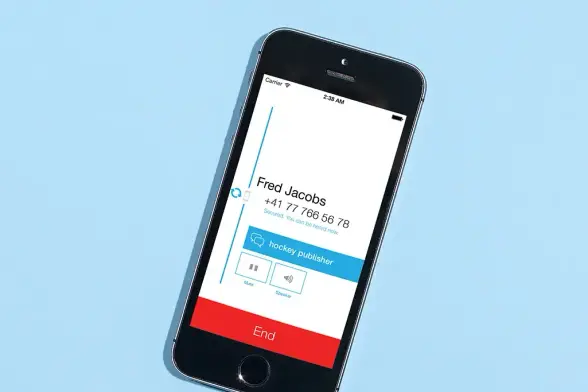
When we shipped Signal 1.0 with ZRTP, those were the words on the display during calls.
👇