Cl0p ransomware extortion gang have a zero day in Oracle E-Business Suite (component: BI Publisher Integration) - which they’ve been exploiting since last month to steal data.
Oracle patches EBS zero-day exploited in Clop data theft attacks
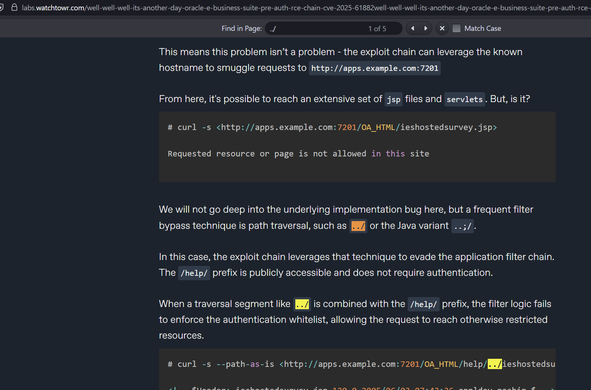
Oracle is warning about a critical E-Business Suite zero-day vulnerability tracked as CVE-2025-61882 that allows attackers to perform unauthenticated remote code execution, with the flaw actively exploited in Clop data theft attacks.