⚠️ Make sure your Podlove Publisher is updated to v4.2.7 (published September 20). It fixes an exploit (published September 22) that is actively being used to upload malicious code to WordPress instances.
Shout out to @ubernauten who went the extra mile to help detect and mitigate attacks for their users.
This post may help you find out if you were affected: https://uberspace.social/@ubernauten/115264495468009257
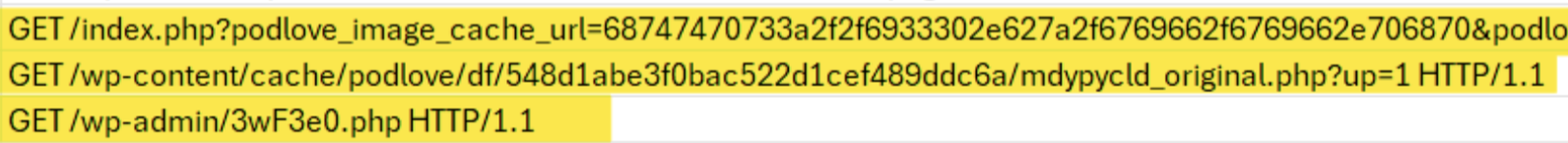
I can now confirm this as I have seen infected instances where wp-admin contained files like `3wF3e0.php` and a `.htaccess` that should not be there.
In http logs, you might see `GET /index.php?podlove_image_cache_url=...`, followed by a call of the exploit file in the cache directory.
–Eric