@leoluk @GossiTheDog For the most part, none of these packages have any need for new versions to appear in anyone's builds for *months* if not years after publication, unless someone *specifically* has read the changes to the new version and sees a new feature they want from it.
LPM platforms should be designed around this basic principle that updates are mostly unwanted.
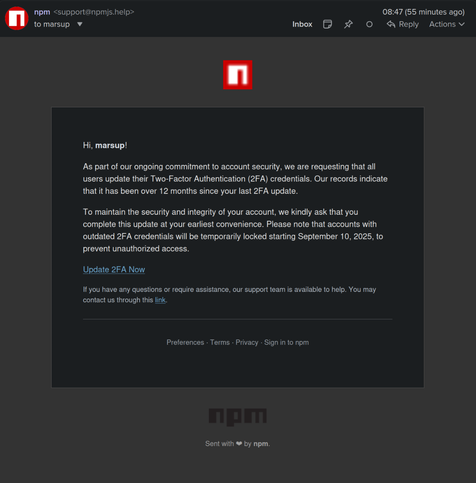
The only way anyone should ever get unexpected updates is if there's a serious security problem, in which case there should be a description of the problem and a small comprehensible patch prominently displayed.
IOW LPMs and similar platforms should behave like Debian Stable.