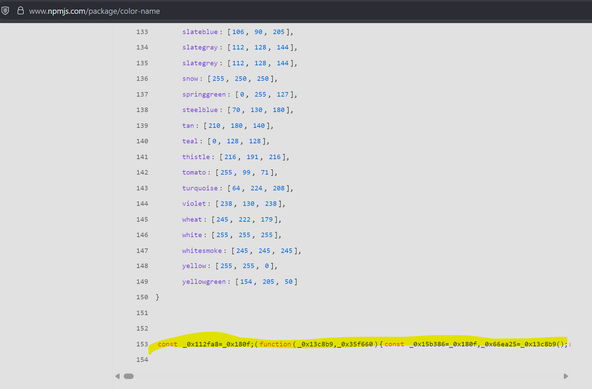
@joby @leoluk @GossiTheDog Or even just copy&paste the 9 lines of code you needed!
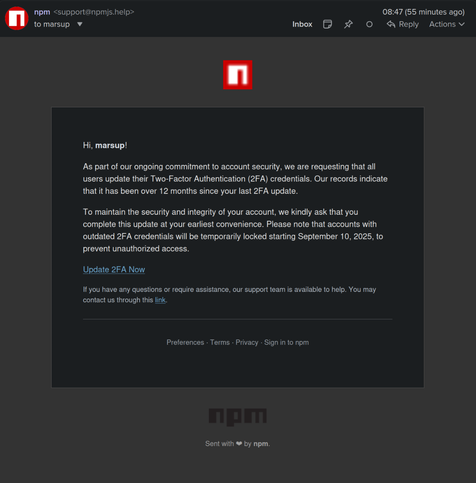
It's about the same amount of code as the interface surface declaring the dependency you needed and binding to it - but without introducing any new interface surface or trust surface!
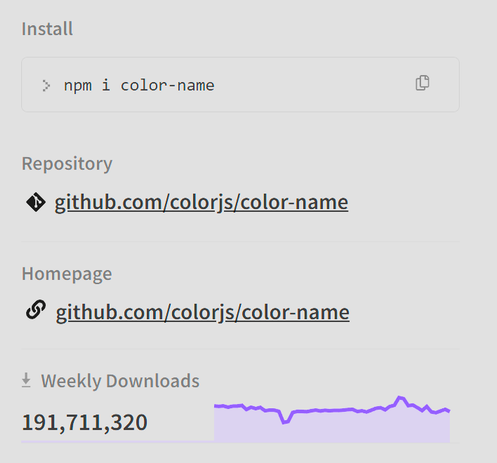
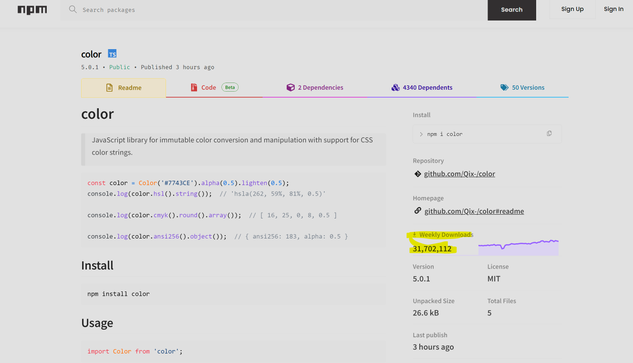
External dependencies that are not c&p into your own code make sense for something large and complex that's likely subject to bugs/fixes, changing requirements of third-party things they interface with, etc. Not for trivial stuff that's a couple lines of js.
 (he/him)
(he/him)