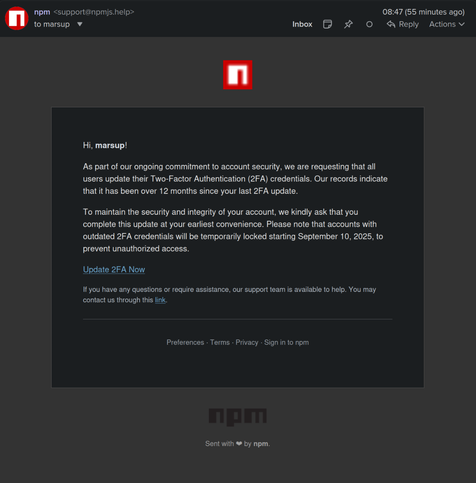
@dalias @leoluk @GossiTheDog @stevel Yeah, at best is could make it noisier, like with the developer receiving at least one email about account updates, which given the phish they could see as normal given those notifications typically don't tell you what was changed.
In fact it also reminds me that I don't think I've ever seen a website actually verify that the emails listed in the OpenPGP key can actually use said key (I would know, one of the entries in mine isn't email but my fediverse ID).
Something which has been the normal workflow for SSL/TLS certificates for decades.