@GossiTheDog Do you have a list of the compromised versions?
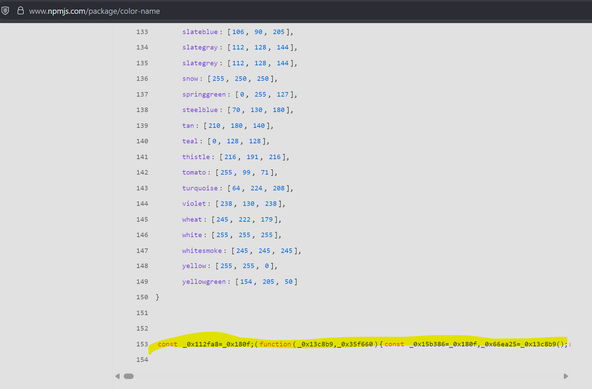
A few of these, when I check I see that the version published this morning is still present and the latest version. But a quick glance at the code and I don't see the compromise; I'm just doing a quick scan, but some of these packages are so simple that there's really not many places you could hide it:
https://www.npmjs.com/package/has-ansi?activeTab=code
I'm just trying to compile a list of compromised versions so I can do a quick scan of our systems, but for some of these I haven't been able to find an exploited version.
Maybe the attackers script failed to insert the exploit, as we do see a number of these packages all updated at the same time, but I don't see the exploit code in them. Packages fitting that pattern:
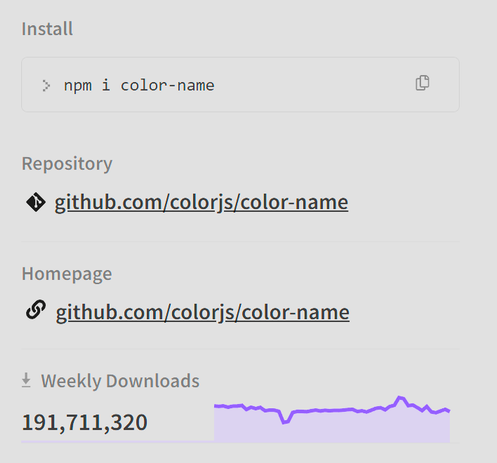
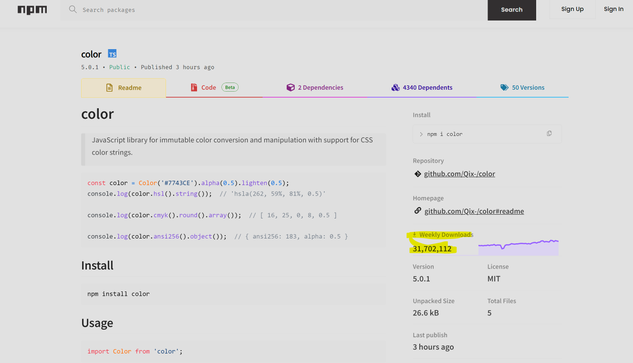
* color
* supports-color
* strip-ansi
* ansi-regex
* has-ansi
(note: all of this is based on a quick glance using the code tab on the NPM registry; it's possible that I could have missed the right file, or missed it when scanning visually, or the code tab might not be showing the version it claims, or the like)