Spring Security: Role-Based Access – Thread 🧵
𝟏) 𝐖𝐡𝐚𝐭 𝐢𝐬 𝐑𝐨𝐥𝐞-𝐁𝐚𝐬𝐞𝐝 𝐀𝐜𝐜𝐞𝐬𝐬 𝐂𝐨𝐧𝐭𝐫𝐨𝐥 (𝐑𝐁𝐀𝐂)?
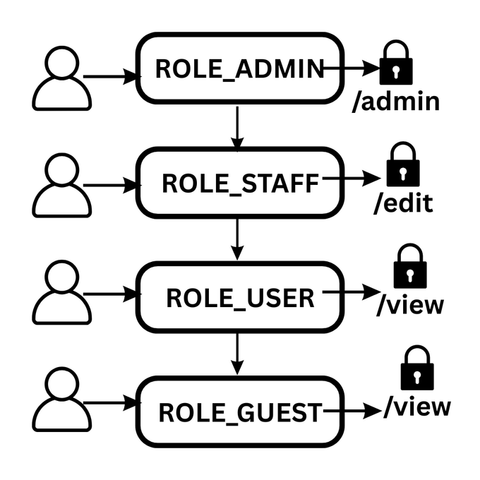
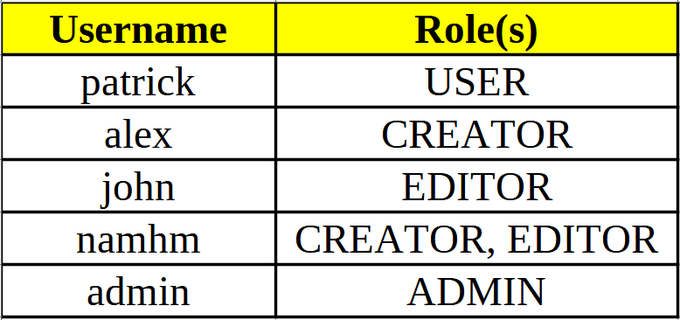
RBAC is a security approach where permissions are assigned to roles, and users are assigned roles. This makes managing permissions simpler and more scalable, especially as your application grows.