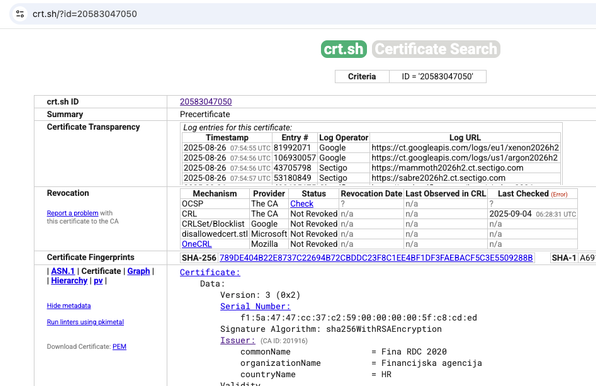
The first rogue 1.1.1.1 certificate was issued by Fina and logged to Certificate Transparency over a year ago.
AFAICT, the first person to notice any of this was Hacker News user JXzVB0iA, two days ago:
https://news.ycombinator.com/item?id=45089708This morning, it was reported to the certificate-transparency mailing list, with attribution to JXzVB0iA.
A few hours later, it was reported to the mozilla-dev-security-policy mailing list, without attribution.
Then Dan Goodin wrote his article, citing the mozilla-dev-security-policy post.
Very surprising that Cloudflare did not notice given they operate a CT monitor.