There’s a bunch of new Netscaler vulns being exploited as zero days. Patches just out now.
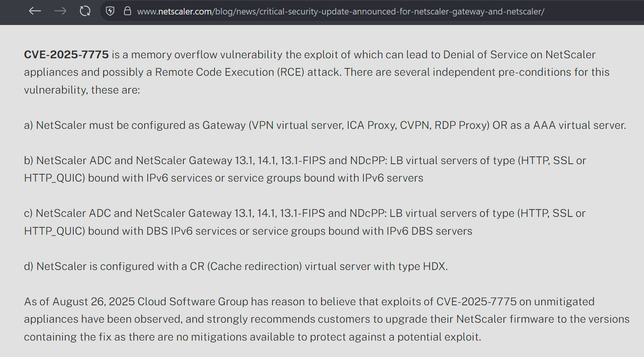
Preauth RCE being used to drop webshells to backdoor orgs. CVE-2025-7775 is the main problem.
Orgs will need to do IR afterwards as technical details emerge of backdoor.