Colt disappeared yesterday, their status page says "technical issue"
Their customer portal is also MIA: https://online.colt.net
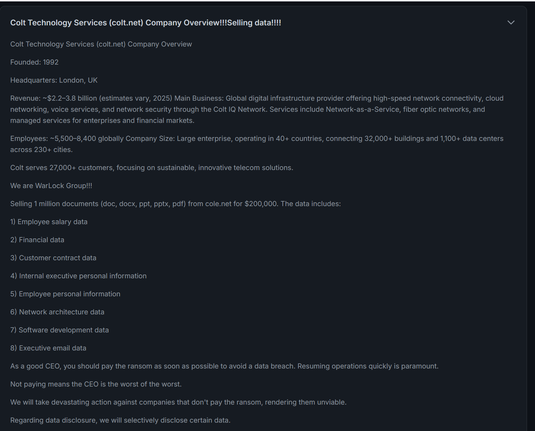
Colt are being extorted by Warlock ransomware group, they have been for over a week, Colt are trying to cover it up.
Entry likely via sharehelp.colt.net via CVE-2025-53770 as they were interacting with it.
They've stolen a few hundred gig of customer data and documentation and posted a file list on a forum.
Colt Telecom attack claimed by WarLock ransomware, data up for sale
UK-based telecommunications company Colt Technology Services is dealing with a cyberattack that has caused a multi-day outage of some of the company's operations, including hosting and porting services, Colt Online and Voice API platforms.
There's apparently a mirror of the Colt file name tree here, for any orgs looking to establish their risk. https://mastodon.social/@casaundra/115033551022266815
There’s another plain text mirror here: https://www.klos.com/~john/colt_filename_tree.txt
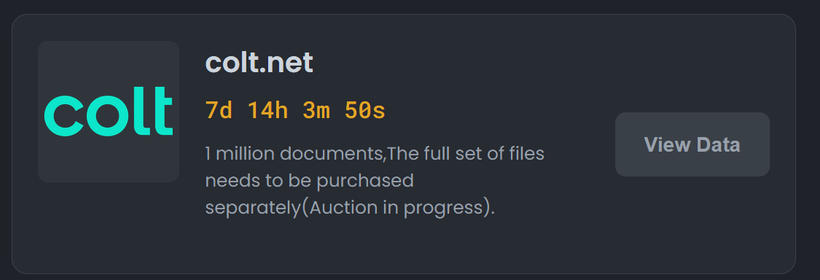
Colt Technology Services are up on the Warlock ransomware group portal.
List of 400k files they have stolen: https://www.klos.com/~john/colt_filename_tree.txt
I’ve authenticated the filenames are real, eg they include customer documentation and performance reviews of Colt staff.
Colt also appears in Warlock's FAQ page, it's an echo of their RAMP forum post with a minor change ("Regarding data disclosure, we will selectively disclose certain data.")
My view is Colt shouldn't pay. It is directly funding organised crime - even if paid for via insurance/legal agents - and increases the risk to everybody else.
Colt have setup a cyber incident page, set to noindex so Google etc can’t find it, detailing their incident.
https://www.colt.net/go/cyber-incident/
Confirms for first time customer documentation stolen and some scope of systems still offline.
The status updates on Colt's website describing a "technical issue" have been removed, replacing it with always being a cyber incident.
Left - internet archive - https://web.archive.org/web/20250814102113/https://www.colt.net/status/
Right - now https://www.colt.net/status/#updates
I've written about the Colt Technology Services ransomware incident, with a focus on learnings for other organisations.
Guest appearance by @leakix for finding the webshell at Colt.
Colt’s status page has been revised, removing most of the prior updates, with a new bolded statement around customer systems. https://www.colt.net/status/
The separate cyber incident page, detailing what happened, isn’t linked anywhere on their website and is set to noindex: https://www.colt.net/go/cyber-incident/
By repeatedly linking the Colt cyber incident page, I have got it into a Google search for Colt cyber incident though - the content is just hidden from search. https://www.colt.net/go/cyber-incident/
We really should be over the point of companies trying to hide their cyber incidents, it’s race to the bottom stuff.