Co-op Group say they have exited containment and begun recovery phase https://www.theguardian.com/business/2025/may/14/co-op-cyber-attack-stock-availability-in-stores-will-not-improve-until-weekend
Marks and Spencer are still in containment
If you want figures for your board to set expectations in big game ransomware incidents, Co-op containment just over 2 weeks, M&S just over 3 weeks so far - recovery comes after.
In terms of external assistance, Co-op have Microsoft Incident Response (DART), KPMG and crisis comms. M&S have CrowdStrike, Microsoft, Fenix and crisis comms.
The threat actor at Co-op says Co-op shut systems down, which appears to have really pissed off the threat actor. This was the right, and smart, thing to do.
While I was at Co-op we did a rehearsal of ransomware deployment on point of sale devices with the retail team, and the outcome was a business ending event due to the inability to take payments for a prolonged period of time. So early intervention with containment was the right thing to do, 100%.
M&S have finally told staff that data about themselves was stolen: https://www.telegraph.co.uk/business/2025/05/16/ms-staff-data-stolen-by-hackers-in-cyber-attack/
You may notice I said they had staff data stolen on May 9th in this thread.
For the record, the tools listed in this article aren't used by Co-op.
The link in the article to Vectra Cognito AI has a Coop Sweden logo on it, and the Coop Sweden CISO is named. Coop Sweden is different company. Coop Sweden went on to have a ransomware attack that crippled the org, including point of sale, so I don't think it's a good sales point. Same with Silverfort.
Google AI has ingested the article and now uses it to claim Co-op Group use the tools.
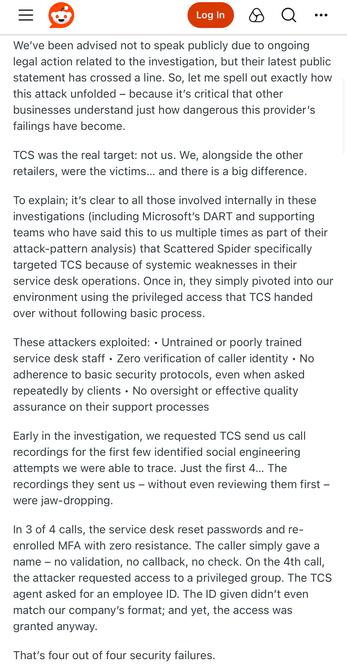
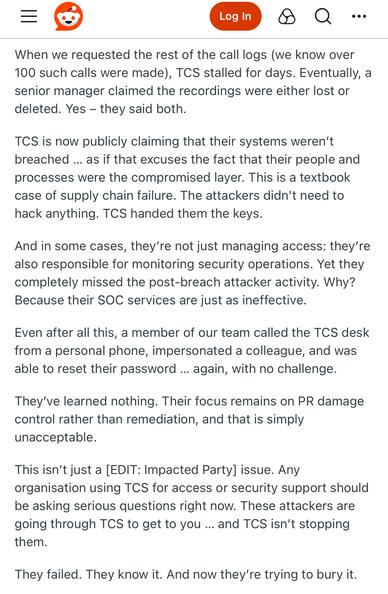
The Times reports M&S were breached through a contractor and that human error is to blame. (Both M&S and Co-op use TCS for their IT Service Desk).
The threat actor went undetected for 52 hours. (I suspect detection was when their ESXi cluster got encrypted).
M&S have told the Times they had no “direct” communication with DragonForce, which is code for they’re using a third party to negotiate - standard practice.
https://www.thetimes.com/uk/technology-uk/article/m-and-s-boss-cyber-attack-7d9hvk6ds
M&S looks to be moving to reposition their incident as a third party failure, which I imagine will help redirect some of the blame (they present their financial results during the week to investors): https://www.bbc.co.uk/news/articles/cpqe213vw3po
Both M&S and Co-op outsourced their IT, including their Service Desk (helpdesk), to TCS (Tata) around 2018, as part of cost savings.
There's nothing to suggest TCS itself have a breach btw.
Basically, if you go for the lowest cost helpdesk - you might want to follow the NCSC advice on authenticating password and MFA token resets.
I've put a 3 part deep dive blog series coming out probably next week called Living-Off-The-Company, which is about how teenagers have realised large orgs have outsourced to MSPs who follow the same format of SOP documentation, use of cloud services etc. Orgs have introduced commonality to surf.
"Cyber analysts and retail executives said the company had been the victim of a ransomware attack, had refused to pay - following government advice - and was working to reinstall all of its computer systems."
Not sure who those analysts are, but since DragonForce haven't released any data and M&S won't comment other than to say they haven't had any "direct" contact with DragonForce, I wouldn't make that assumption.
There's also a line in the article from an cyber industry person saying "if it can happen to M&S, it can happen to anyone" - it's ridiculous and defeatist given Marks and Spencer haven't shared any technical information about how it happened, other than to tell The Sunday Times it was "human error"
The Air Safety version of cyber industry would be a plane crashing into 14 other planes, and industry air safety people going "Gosh, if that can happen to British Airways it could happen to anybody!"
Tomorrow it’s one month since Marks and Spencer started containment, it’s also their financial results day.
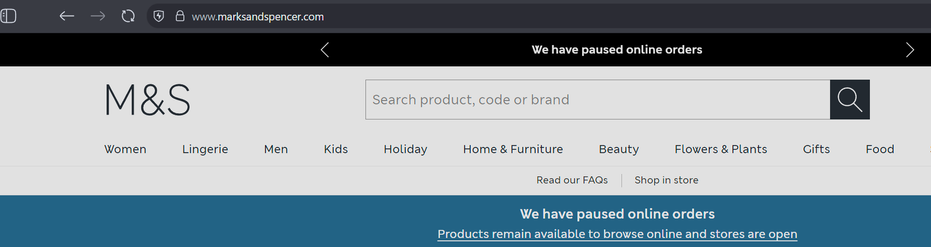
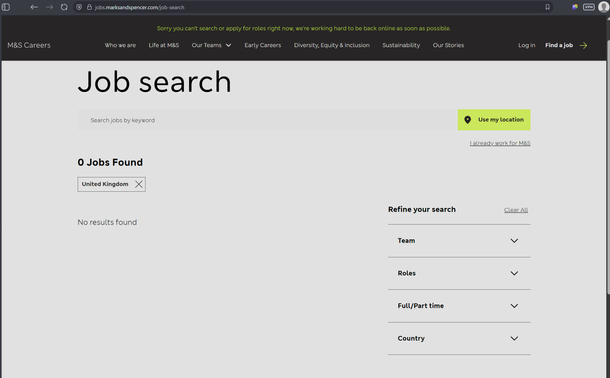
Online ordering still down, all recruitment stopped, Palo-Alto VPNs still offline.
TCS have been linked to the Marks and Spencer breach, at least in part.
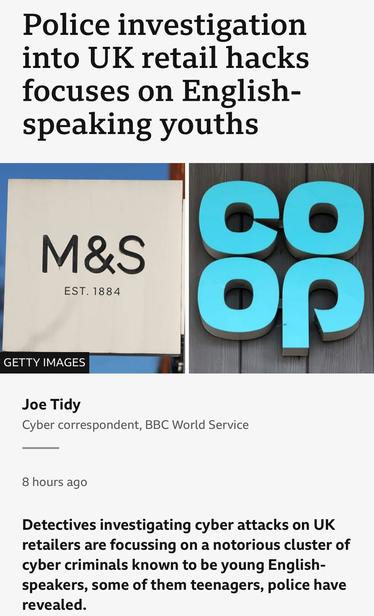
The NCA has confirmed on the record that the investigation into the M&S and Co-op hack is focused on English teenagers. I could toot the names of the people I think they’ll pick up, but won’t.
TCS has a security incident running around the M&S breach.
Interestingly the source claims TCS aren't involved in Co-op's IT - which is categorically false, they took over most of it while I worked there, including the helpdesk, and my team (SecOps) after I left.
https://www.ft.com/content/c658645d-289d-49ee-bc1d-241c651516b0
Insurance Insider say Co-op Group have no cyber insurance policy.
It’s got the insurance industry hard as they think they can ambulance chase other orgs with it.
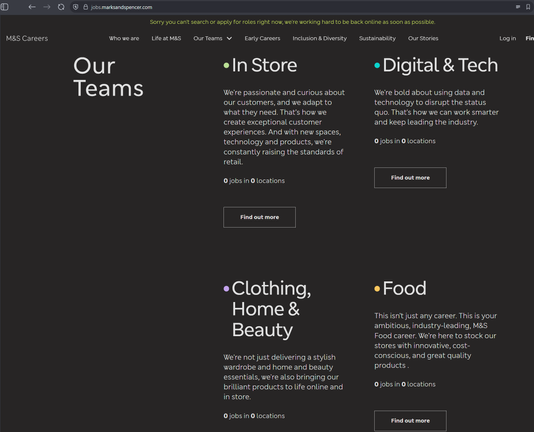
While Co-op have restored every customer facing system and internal systems like recruitment and remote working, M&S still don't even have recruitment back.
I'm reliably told they paid the ransom, so they'll be target #1 basically forever with other ransomware groups now due to resiliency woes and willingness to pay.
https://www.bbc.co.uk/news/articles/c23mz5eg091o
This Daily Mail piece about security leaders thinking work-from-home means they will be crippled is horseshit, I'm not linking it.
They've taken a survey about how security people think their businesses couldn't survive ransomware, and linked it to working from home. WFH isn't the problem: business IT and resilience being built on quicksand is the problem.
Co-op say they have largely completed recovery, and have removed the cyber attack banner and statement from their website
https://www.retailgazette.co.uk/blog/2025/06/co-op-cyber-attack/
I think they did a great job. They do call it a "highly sophisticated attack", which, frankly.. isn't true and may come out in open court later if the suspects are ever caught.
6 weeks from containment to "near full" recovery, for statto nerds like me who track this stuff.
M&S had their ransomware incident communicated via internal email - from the account of a staff member who works for TCS.
The way TCS work is you give them accounts on your AD.
Marks and Spencer have started partial online shopping again.
For statto nerds, around 7 weeks from containment to partial recovery
TCS have told shareholders their systems were not compromised in the hack of M&S.
As an explainer here (not in the article): TCS IT systems weren't compromised. Their helpdesk service (they're AD admins at M&S) was used to gain access to M&S. They manage M&S IT systems.
https://www.reuters.com/business/media-telecom/indias-tcs-says-none-its-systems-were-compromised-ms-hack-2025-06-19/
Latest Marks and Spencer update is pretty crazy.
M&S haven't been able to supply sales data - so the British Retail Consortium (BRC) - used by the UK government as as economic indicator - basically made up figures for M&S and didn't tell people they had done this.
https://www.telegraph.co.uk/business/2025/06/24/retail-lobby-group-accused-of-ms-cyber-cover-up/
Marks and Spencer’s CEO says half of their online ordering is still offline after their ransomware incident, they hope to get open in next 4 weeks.
They are also rebuilding internal systems and hope a majority of that will be done by August.
Lesson: mass contain early. M&S didn’t. Co-op did.
17 and two 19 year old teens picked up over Co-op and M&S hacks, and a 20 year old woman.
Pretend to be surprised.
https://www.occrp.org/en/project/narcofiles-the-new-criminal-order/inside-job-how-a-hacker-helped-cocaine-traffickers-infiltrate-europes-biggest-ports
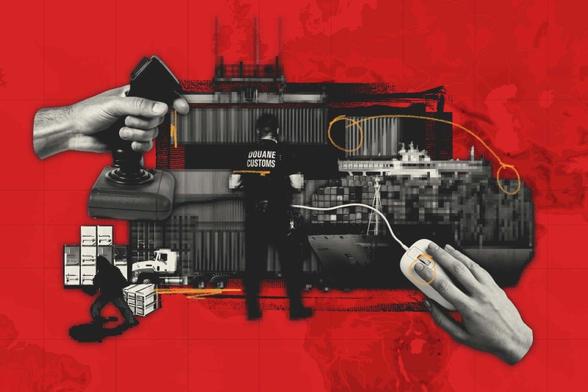
Inside Job: How a Hacker Helped Cocaine Traffickers Infiltrate Europe’s Biggest Ports
Europe’s commercial ports are top entry points for cocaine flooding in at record rates. The work of a Dutch hacker, who was hired by drug traffickers to penetrate port IT networks, reveals how this type of smuggling has become easier than ever.