This is a build upon Huntress' (excellent) blog https://www.huntress.com/blog/threat-advisory-oh-no-cleo-cleo-software-actively-being-exploited-in-the-wild
i would fully pull the plug on impacted Cleo products until there's vendor clarity btw
Shodan dork (not exhaustive) - the Windows ones are a particular problem in terms of ransomware.
https://beta.shodan.io/search?query=http.html_hash%3A1534766930
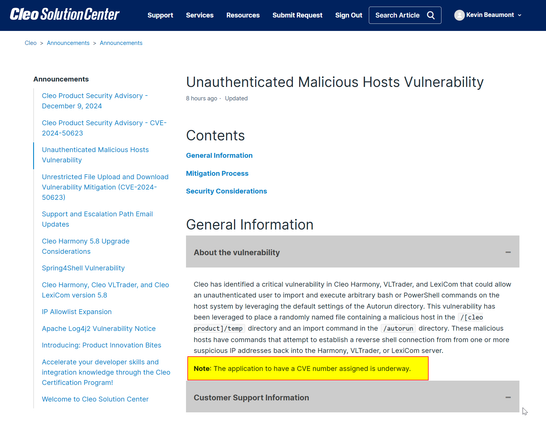
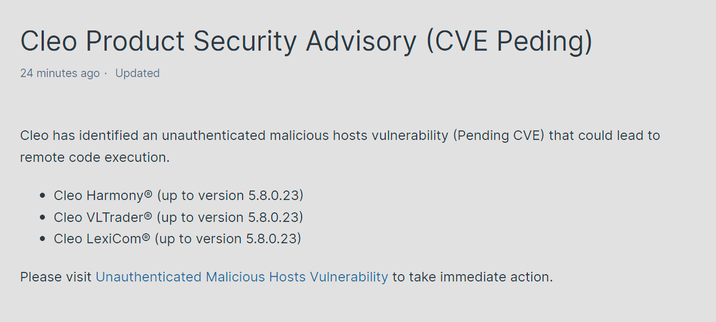
Cleo have issued a (paywalled) advisory about the zero day, saying a new CVE number is being allocated.
Rapid7 say "As of December 10, Rapid7 MDR has confirmed successful exploitation of this issue in customer environments; similar to Huntress, our team has observed enumeration and post-exploitation activity and is investigating multiple incidents." https://www.rapid7.com/blog/post/2024/12/10/etr-widespread-exploitation-of-cleo-file-transfer-software-cve-2024-50623/
After my toot Cleo have issued a public advisory, they're saying versions up to 5.8.0.23 (not out yet) are impacted.
In terms of threat intel, the ransomware operators I know of only have an exploit for the Windows versions, not Linux.
https://support.cleo.com/hc/en-us/articles/28408134019735-Cleo-Product-Security-Advisory-CVE-Peding
"In an emailed statement given to TechCrunch, Jorge Rodriguez, SVP of product Development at Cleo, said that a patch for the critical vulnerability is “under development.”
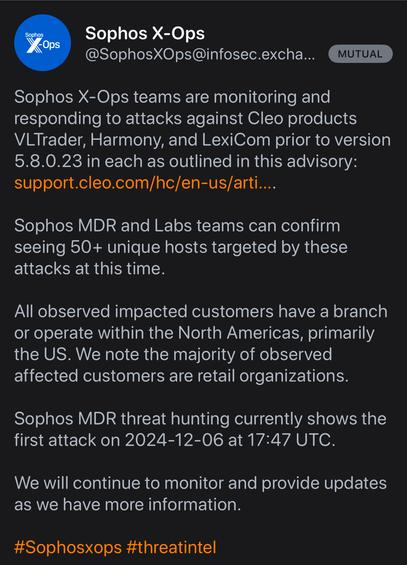
Sophos says they have seen 50+ systems with Cleo enterprise file transfer product zero day exploitation. Huntress say 28+ customers so far. Rapid7 haven’t given numbers.
Sophos X-Ops (@[email protected])
Sophos X-Ops teams are monitoring and responding to attacks against Cleo products VLTrader, Harmony, and LexiCom prior to version 5.8.0.23 in each as outlined in this advisory: https://support.cleo.com/hc/en-us/articles/28408134019735-Cleo-Product-Security-Advisory-CVE-Pending. Sophos MDR and Labs teams can confirm seeing 50+ unique hosts targeted by these attacks at this time. All observed impacted customers have a branch or operate within the North Americas, primarily the US. We note the majority of observed affected customers are retail organizations. Sophos MDR threat hunting currently shows the first attack on 2024-12-06 at 17:47 UTC. We will continue to monitor and provide updates as we have more information. #Sophosxops #threatintel
A writeup on the Cleo vulnerabilities, which are under mass exploitation now. Write any file into any folder by using path=..\..\..\ - since it's a webapp, just drop a webshell.
Cleo Harmony, VLTrader, and LexiCom - RCE via Arbitrary File Write (CVE-2024-50623)
We were having a nice uneventful week at watchTowr, when we got news of some ransomware operators using a zero-day exploit in Cleo MFT software - namely, LexiCom, VLTransfer, and Harmony - applications that many large enterprises rely on to share files securely. Cleo have a (paywalled) advisory, linked to
Another write up on the Cleo zero day: https://arcticwolf.com/resources/blog/cleopatras-shadow-a-mass-exploitation-campaign/
Cleopatra’s Shadow: A Mass Exploitation Campaign Deploying a Java Backdoor Through Zero-Day Exploitation of Cleo MFT Software - Arctic Wolf
Key Takeaways Cleo MFT products were exploited by threat actors to deploy a malicious PowerShell stager, culminating in the execution of a Java-based backdoor we are dubbing Cleopatra. The campaign began on 7 December 2024, and is ongoing as of the publication of this article. The Cleopatra backdoor supports in-memory file storage and is designed ... Cleopatra’s Shadow: A Mass Exploitation Campaign Deploying a Java Backdoor Through Zero-Day Exploitation of Cleo MFT Software
I think the Cleo thing shows the industry and community working very well, btw.
From zero day in an MFT product to approx 2/3rd of servers now offline or patched in days. As far as I know, since mass exploitation began (important caveat) none of the victims had follow on activity, ie ransomware.
That’s a really good outcome. The reason, I think, is openness and transparency - Huntress went public early and everybody leaped on it loudly in the community. Be more open.