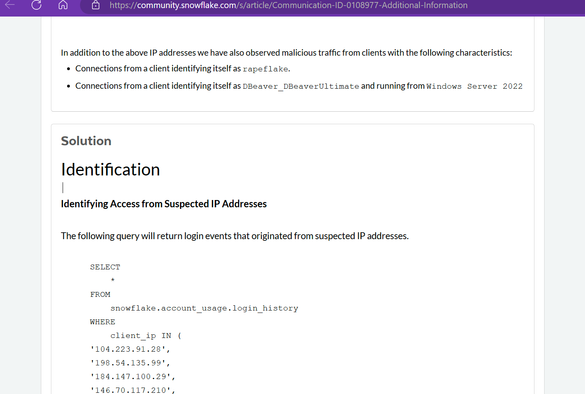
Snowflake: there is absolutely no cybersecurity incident.
Also Snowflake: Please run these commands and look for "threat activity" logins with the user agent "rapeflake" using this knowledge base article we haven't listed on our website.
https://community.snowflake.com/s/article/Communication-ID-0108977-Additional-Information
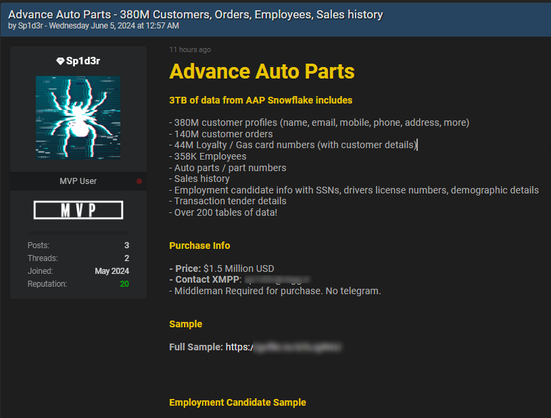
Live Nation said its stolen database was hosted on Snowflake, a cloud storage and analytics company.
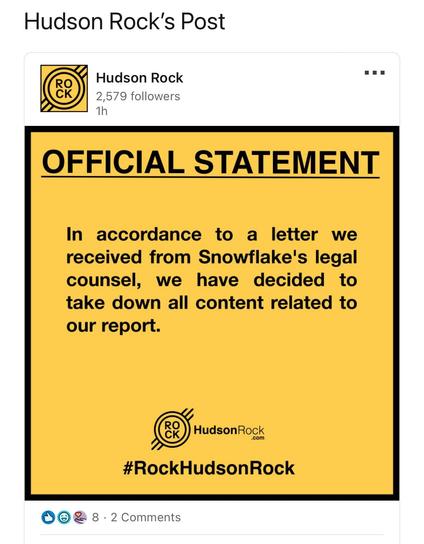
The deleted Hudson Rock post on Snowflake breach: https://web.archive.org/web/20240531140540/https://hudsonrock.com/blog/snowflake-massive-breach-access-through-infostealer-infection
For the record I don't think all the content is accurate - however Snowflake did have a security incident via their former employee, they have full IR stood up. They didn't follow their own best practices.
I also know multiple orgs who've had their full databases taken from Snowflake.
The Snowflake authentication setup is terrible.
MFA can’t be enabled org wide, each user has to manually log in and enable it. There’s no policy to block users without MFA. And it uses Duo MFA rather than your orgs MFA. (You can bring your own MFA with SAML).
Also all users log in via a Snowflake domain, so you can just pull creds from info stealer marketplaces or logs.
That’s why they’re being targeted as a platform.
IMHO it's fair to call out Snowflake's authentication isn't very good - it's the worst SaaS MFA solution I've seen as it has no top level, easy switch for org wide MFA enforcement.
Combined with putting all customers under *.snowflakecomputing.com sub domain is why their customers are getting owned - infostealers are just full of creds ready to go.
I gather Snowflake are discussing changes to fix, don't tell the fanboys (and yes, they're all dudes).
Mandiant have informed 165 organisations they may have had data exfiltration from their Snowflake hosted databases
https://cloud.google.com/blog/topics/threat-intelligence/unc5537-snowflake-data-theft-extortion/
✅ won a game of Call of Duty
✅ hacked the world’s largest companies
✅ used an infostealer
Can’t wait for these guys to have super secure Microsoft Recall, which is definitely encrypted from the user 🤪🤪🫡
Snowflake have told customers "We are also developing a plan to require our customers to implement advanced security controls, like multi-factor authentication (MFA) or network policies, especially for privileged Snowflake customer accounts."
Good! They also say the attack was "not caused by a vulnerability, misconfiguration, or breach of its product". Just happy little bad MFA.
Nice: "In a phone call this week, Jones (Snowflake CISO) told WIRED that Snowflake is working on giving its customers the ability to mandate that users of their accounts employ multifactor authentication going forward, “and then we’ll be looking in the future to [make the] default MFA,” he says."
This will be a great outcome for Snowflake customers and Snowflake itself. I know Snowflake got big mad at me for pointing it out, but that was a prime weakness in their MFA.
https://www.wired.com/story/epam-snowflake-ticketmaster-breach-shinyhunters/
Snowflake isn’t an outlier, it’s the canary in the coal mine
By Nick Biasini with contributions from Kendall McKay and Guilherme Venere Headlines continue to roll in about the many implications and follow-on attacks originating from leaked and/or stolen credentials for the Snowflake cloud data platform. Adversaries obtained stolen login credentials for Snowflake accounts acquired via information-stealing malware and used
I think SaaS providers who provide their own authentication have a responsibility to provide robust, *enforceable* MFA for their customers - so if an org wants all their users to require MFA, they can and it’s just an easy tick box.
Some SaaS providers aren’t doing this - - and it’s the reason infostealer logs are such a problem. Their angle is customer is solely responsible, but as a counterpoint: see how that is working out for Snowflake.
Snowflake have rolled out MFA changes:
- A new authentication policy that requires MFA for all users in a Snowflake account
- prompting for user-level MFA setup
- Snowflake Trust Center for monitoring adherence to MFA policies
This solves all the inherent product weaknesses from the prior setup, they did a good job.
https://www.snowflake.com/blog/snowflake-admins-enforce-mandatory-mfa/
The person who got arrested for this is likely a kid btw, there’s a bunch on Telegram who operate with terrible OPSEC.
Turns out yeeting your most sensitive data into a “AI Data Cloud” with no enforceable (at the time) MFA was a bad idea.
An observation - AT&T, which today announced the biggest data breach of any telco worldwide ever - is down 0.35% on stock market
Snowflake, who own the SaaS platform, are down another 2%, 15% down over 3 months
Each breach has driven Snowflake’s share price down, but not their customer’s share price
In other words: 2024 reality, if you’re a SaaS provider, infostealers and cyber crime groups are a competitor - you have to be shit hot at authentication (even if it inconveniences the customer)
The AT&T Snowflake database wasn’t a law enforcement database, that is false.
They’re a major Snowflake customer, they put CDR in to do data analysis.
They subscribe to Snowflake Telecom Data Cloud and push petabytes of data in, as do other telcos. Snowflake had no way to mandate MFA on local accounts (that is fixed now).
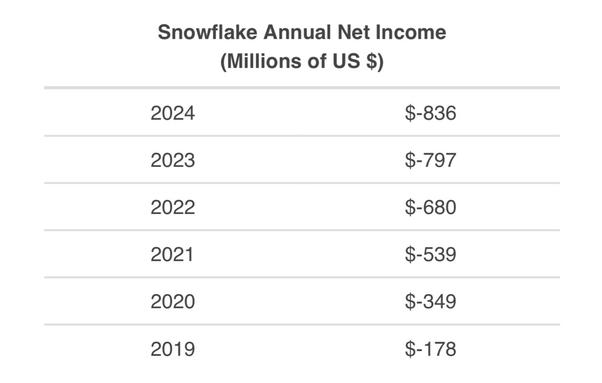
The latest Snowflake quarterly results dropped on Wednesday so I looked at their investor presentation, to see what they said about the security incident.
Nothing.
The company's net loss widened to $317 million, from $227 million during the same period a year earlier but this isn’t unusual, they have had accelerated losses for some time.
More smart changes by Snowflake
MFA enforced on all accounts and all new sign ups
Long term plan to go passwordless for authentication (or rather no single factor password auth)
https://www.snowflake.com/en/blog/multi-factor-identification-default/
(for non italian speking folks please use a translator)
IERI, QUELLO CHE È SUCCESSO A GOOGLE, NON È STATO IL PRIMO CASO DI "EFFETTO VALANGA" - Lo spiega un manuale di O'Reilly (no, non è "Oh'Really?") a cura di... Google:
CAPITOLO 1 L'intersezione tra sicurezza e affidabilità Di Adam Stubblefield, Massimiliano Poletto, e Piotr Lewandowski con David Huska e Betsy Beyer Su password e trapani elettrici Il 27 sett…