Wild, true story from the security awareness and training company KnowBe4 that details how they inadvertently hired a North Korean hacker who was posing as a Western tech worker.
Kudos to them for publishing this. If it can happen to a security awareness company, it can happen to anyone (full disclosure: they've been an advertiser on my site for ages).
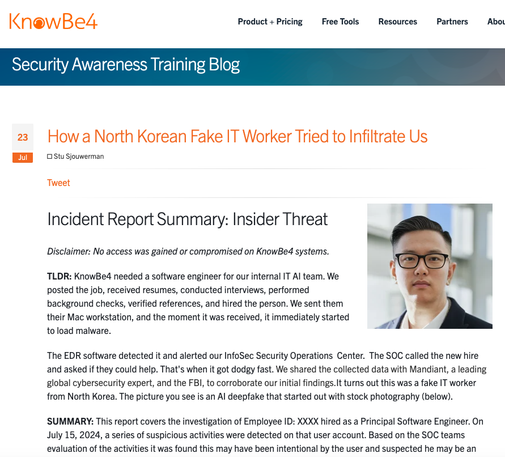
https://blog.knowbe4.com/how-a-north-korean-fake-it-worker-tried-to-infiltrate-us