HID: the most abused protocol
- U2F/FIDO security keys
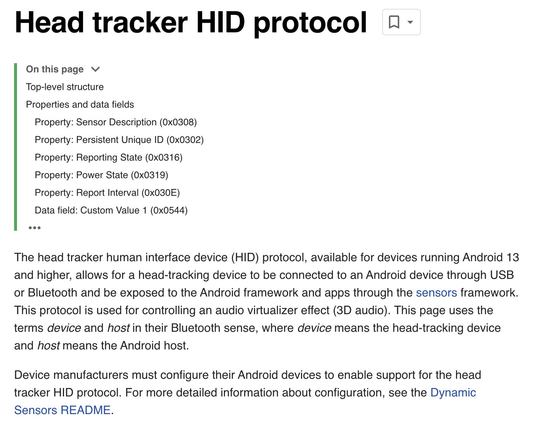
- head tracking
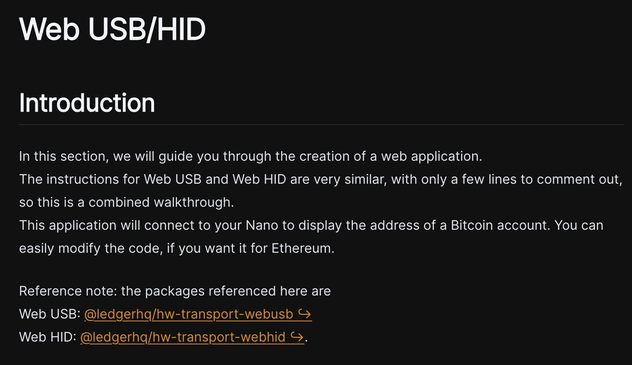
- hardware crypto wallets
- fan controllers
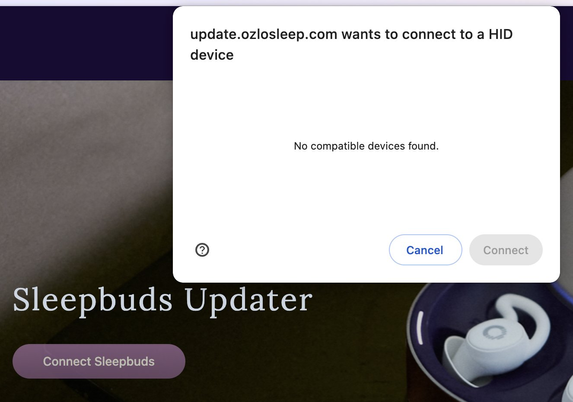
- earbuds firmware update
- U2F/FIDO security keys
- head tracking
- hardware crypto wallets
- fan controllers
- earbuds firmware update