Very big cyber incident playing out at Snowflake, who describe themselves as “AI Data Cloud”. They have a free trial where anybody can sign up and upload data… and they have.
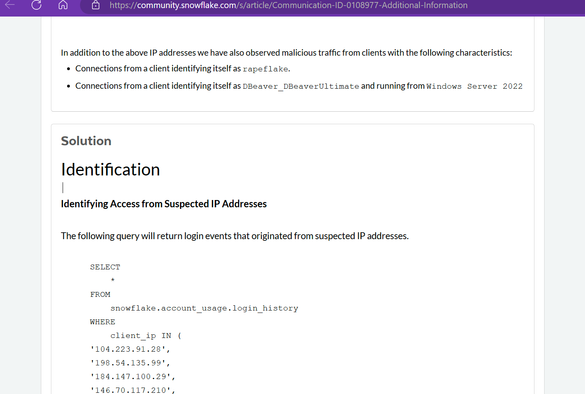
Threat actors have been scraping customer data using a tool called rapeflake, for about a month.