Just published the second-longest blog post in my 14 year career as an independent reporter.
This story is the result of a ridiculous amount of research. I hope you like it, because I learned tons reporting this, and there needs to be a broader conversation about some of the issues raised by this research. The lede:
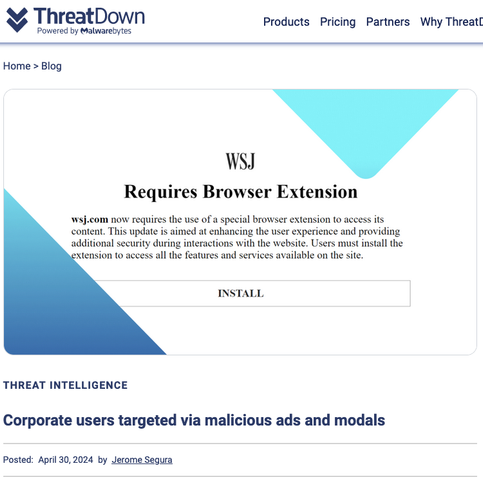
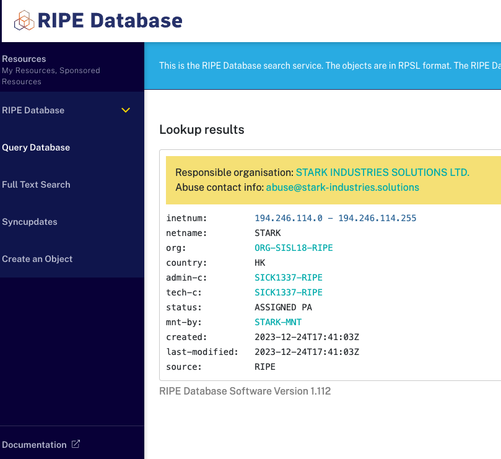
Two weeks before Russia invaded Ukraine in February 2022, a large, mysterious new Internet hosting firm called Stark Industries Solutions materialized and quickly became the epicenter of massive distributed denial-of-service (DDoS) attacks on government and commercial targets in Ukraine and Europe. An investigation into Stark Industries reveals it is being used as a global proxy network that conceals the true source of cyberattacks and disinformation campaigns against enemies of Russia.
https://krebsonsecurity.com/2024/05/stark-industries-solutions-an-iron-hammer-in-the-cloud/