Scoop: I obtained the contract Samsung requires independent shops to sign to buy phone repair parts from them.
It requires:
- "Daily" dumps of customer data
- The "immediate destruction" of any phones a shop comes across that has third-party parts
Scoop: I obtained the contract Samsung requires independent shops to sign to buy phone repair parts from them.
It requires:
- "Daily" dumps of customer data
- The "immediate destruction" of any phones a shop comes across that has third-party parts
@Anibyl @jasonkoebler Most alternate mobile operating systems greatly reduce security including the security against data extraction from the device, remote attacks, apps, etc. GrapheneOS does the opposite.
We greatly improve the defenses against that attack vector, but in this case it sounds like users are providing their lock method. Samsung does have working always-enabled encryption but Cellebrite, etc. can bypass it unless the device is Before First Unlock with a strong passphrase.
@Anibyl @jasonkoebler See https://grapheneos.social/@GrapheneOS/112462758257739953 in our recent thread about how GrapheneOS and other devices are holding up against this attack vector. Nearly all other alternate operating systems are reducing security, not improving it, so your statement is overly general.
There's no evidence of backdoors in Samsung devices but rather they are simply a lot easier to exploit than GrapheneOS. They lack proper alternate OS support so another OS would be missing important security features.
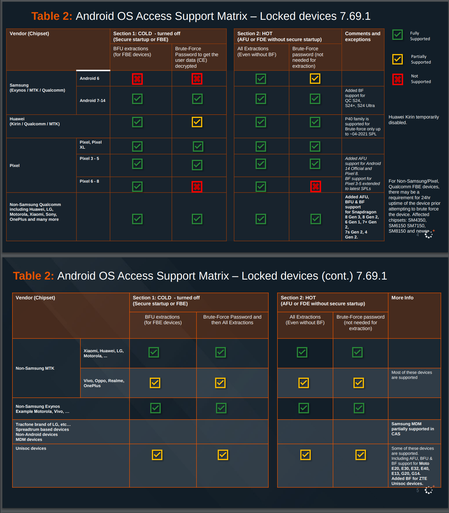
Attached: 2 images Cellebrite's list of capabilities provided to customers in April 2024 shows they can successfully exploit every non-GrapheneOS Android device brand both BFU and AFU, but not GrapheneOS if patch level is past late 2022. It shows only Pixels stop brute force via the secure element.