'What your phone won’t tell you' now @ #37c3 https://streaming.media.ccc.de/37c3/eins details https://fahrplan.events.ccc.de/congress/2023/fahrplan/events/11868.html
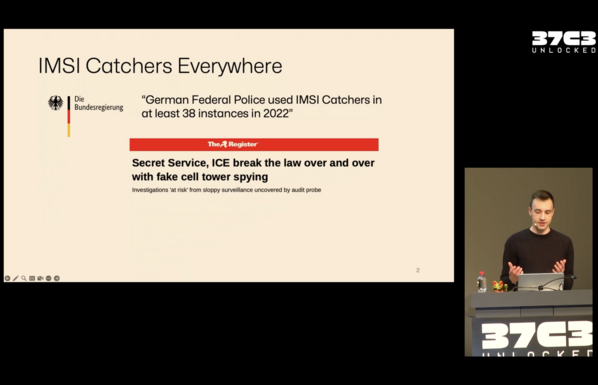
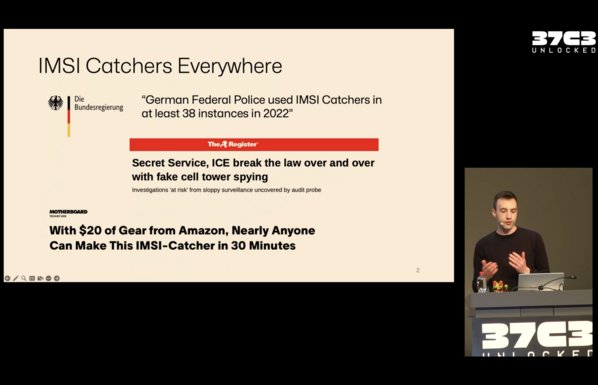
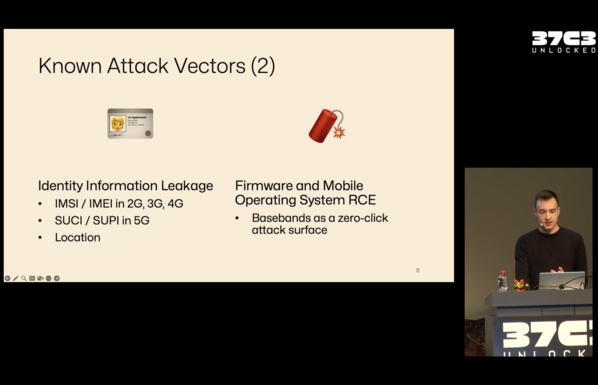
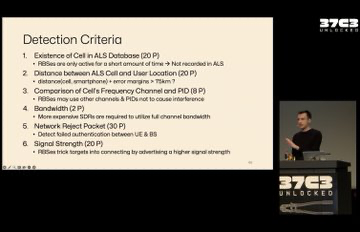
IMSI catchers are used by DE gov. No way to detect via phone (currently).
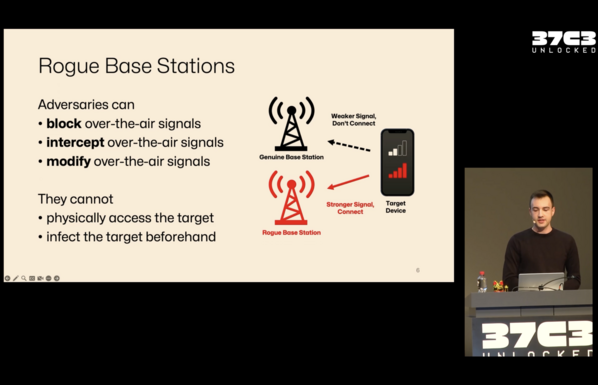
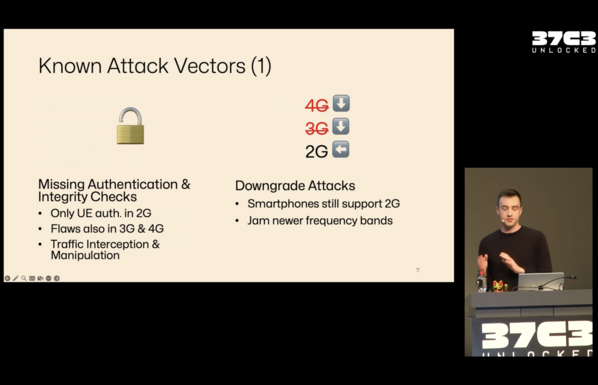
Usual attacks are downgrade attacks (2G). Avoid this by disallowing 2G. 5G there are some improvements. Firmware and OS attacks are still possible.
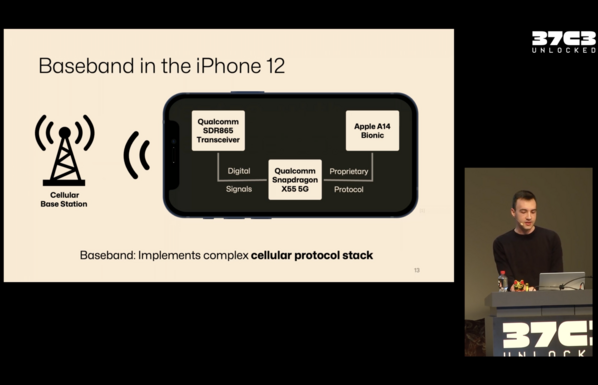
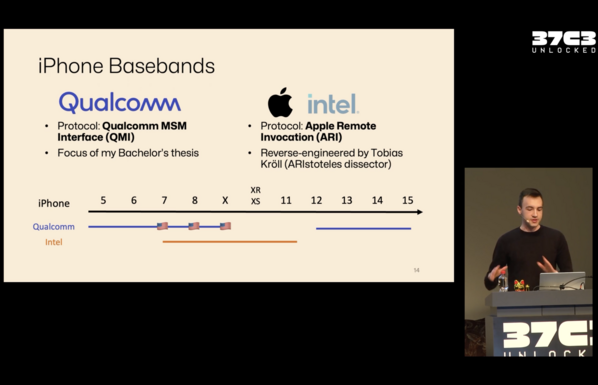
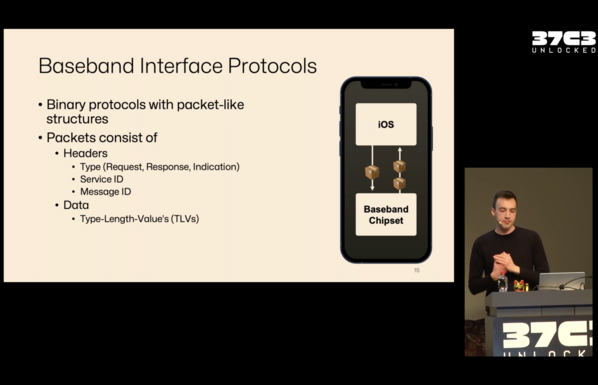
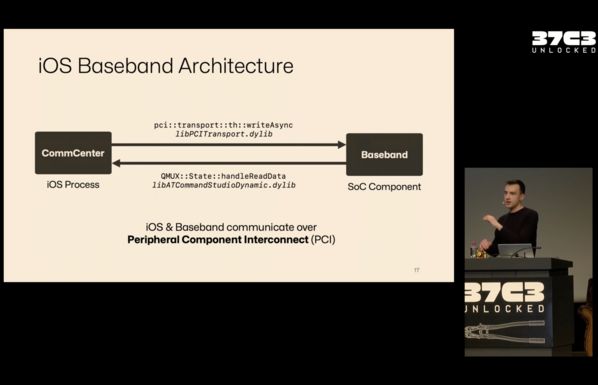
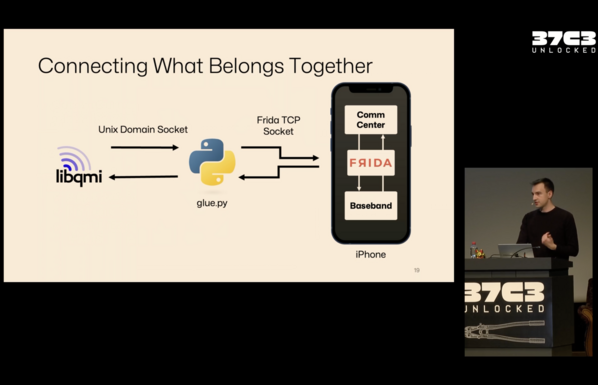
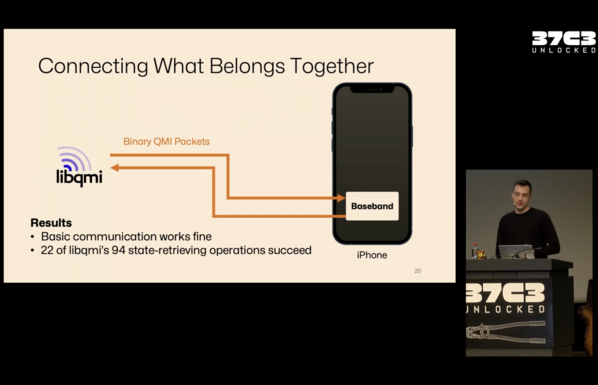
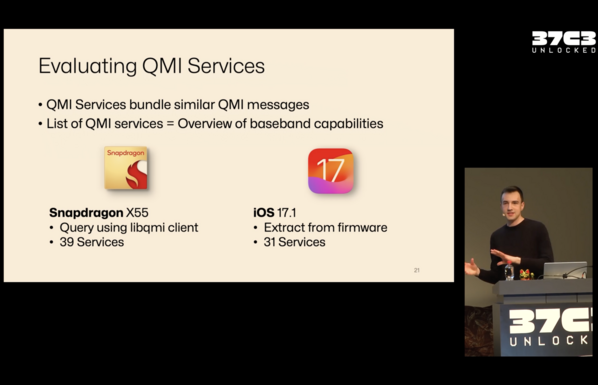
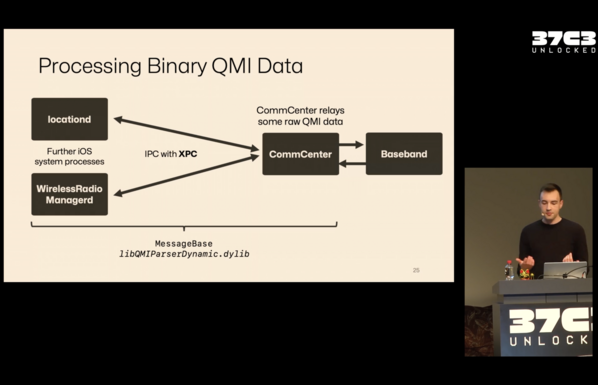
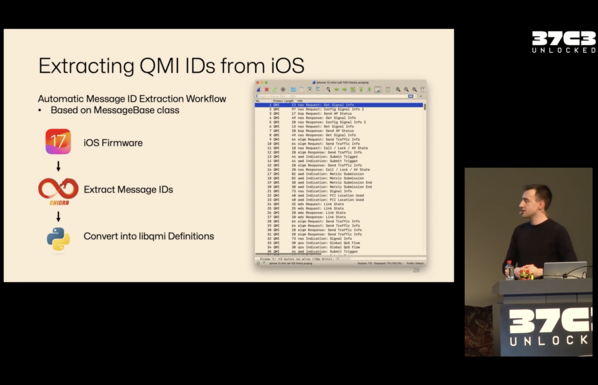
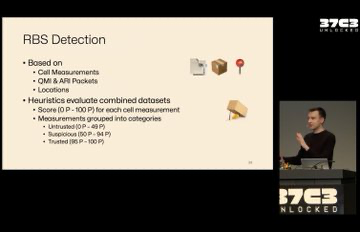
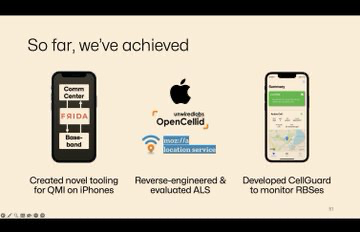
QMI .. not public. LibQMI includes some details.
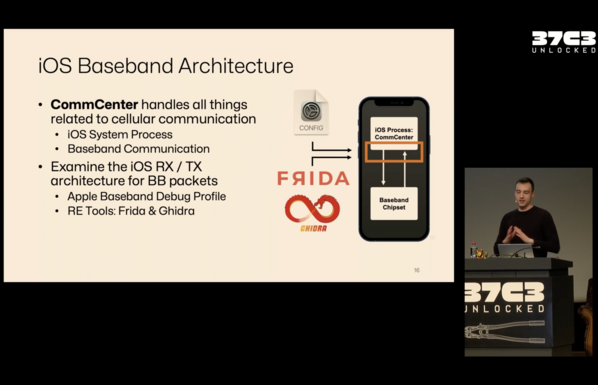
CommCenter is making an appearance again. @jiska has done more work here.
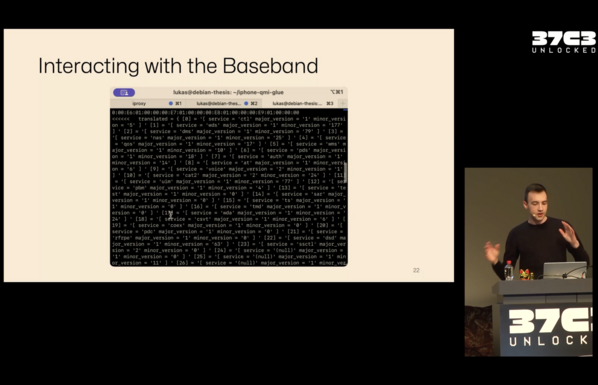
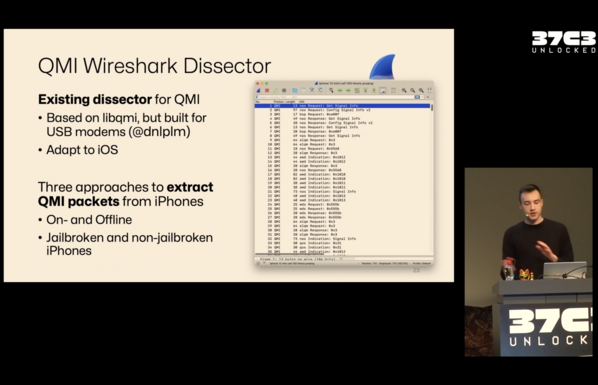
All QMI service can be queried (using LibQMI). Capabilities are returned. Wireshark plugin adapted for iOS
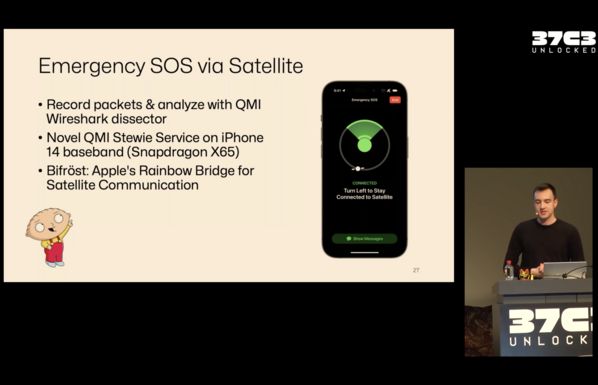
Using Frida these were found. Satellite comms can be inspected.
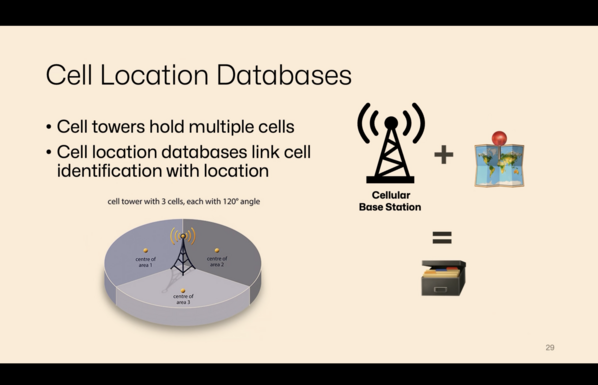
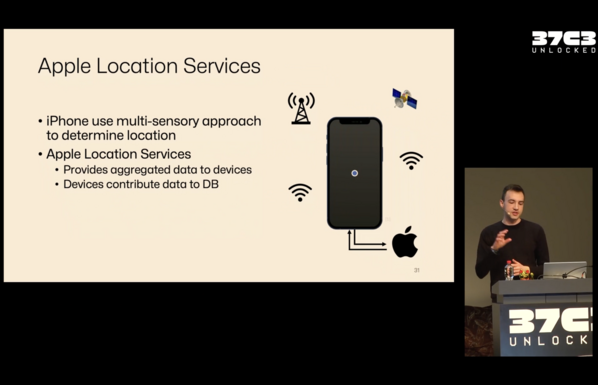
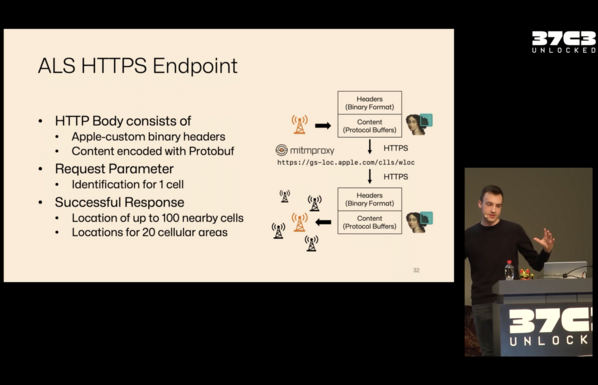
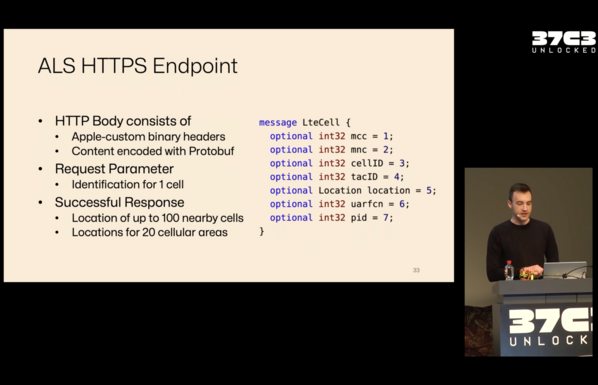
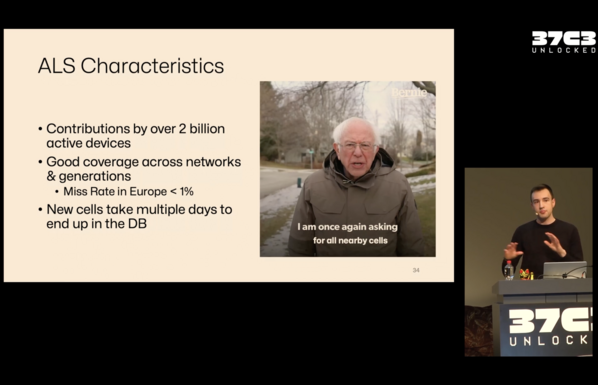
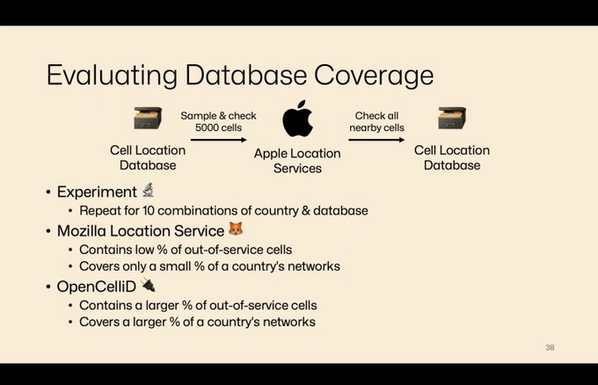
Cell tower IDs can provide a location. Apple always updating DB.
There are open source location services.
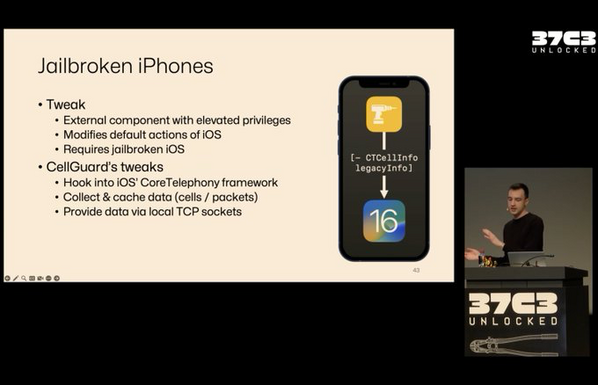
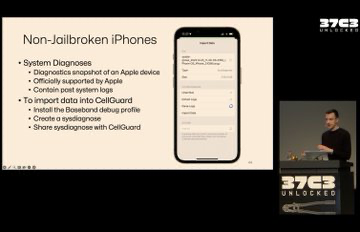
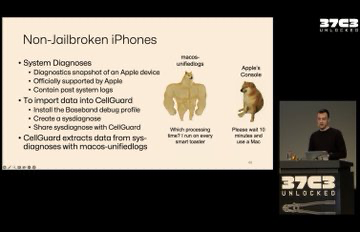
Jailbroken and non-jailbroken phones to run CellGuard.
You can see all the cell info and all cells. A lot of information is shown. Not sure which version (jailbroken or not)
How can you confirm that there is a rogue cell ? The team was not able to confirm finding one. Not ready for release, yet.
Q: Is 5G more secure? A: Yes, 5G is more secure.
Q: Is it possible to create a Rogue cell with the same ID ? A: Yes, some attacks do this. This is more work to be done here.
Q: Is it possible to query the database without and Apple phone ? A: Created a Python script, add cell id and get a list of them. No auth. So possible to get the data.
Q: Is it possible to write data to Apple's service. A: Team things there are different services. (R,W)
Q: Rogue cells were looked at but what about normal stations ? A: Found that some kind of errors happen when moving too fast. Mobile stations are also an issue. This is why release is delayed.