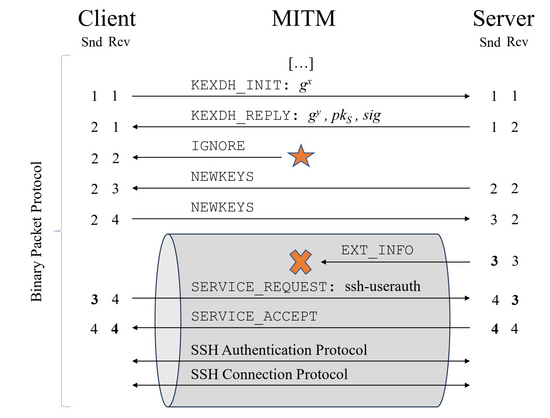
We found a flaw in the SSH specification which allows a MitM attacker to drop certain messages from the secured connection. If you are using SSH, check this out: https://terrapin-attack.com 🐢
Joined work with Fabian Bäumer and Jörg Schwenk at Ruhr University Bochum, HGI, funded by CASA Excellence Cluster / DFG.