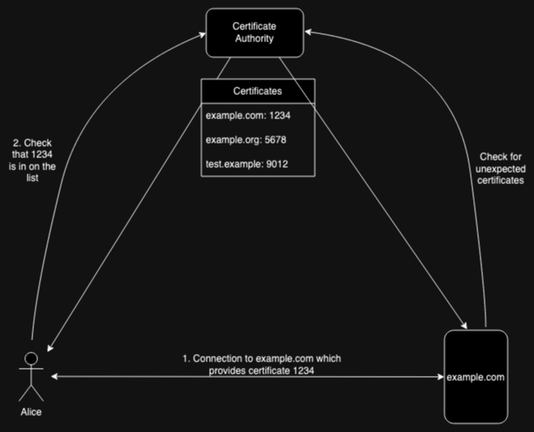
The first step is to have the client (i.e., the browser) check that the certificate was published, thus hopefully forcing the CA to publish it. But now we have to confront the definition of "publish". How do we know the CA published to everyone?
For instance, if the CA has it on their web site and sends it to clients but not to sites when they check, then the system breaks down.
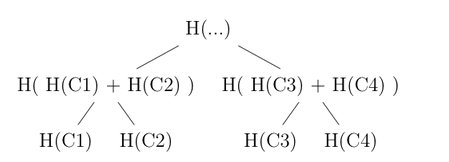
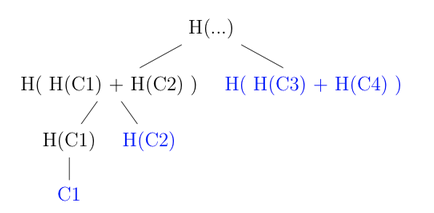
The standard solution here is what's called a consensus system. Effectively, you compute a summary of all the published certificates (typically by assembling them into a Merkle hash tree). See the post for more detail on this.
Next, you need some mechanism whereby each element in the system can assure itself that it has the same summary as everyone else (this is actually the hard part).
Next, you need some mechanism whereby each element in the system can assure itself that it has the same summary as everyone else (this is actually the hard part).
Finally, when you go to the Web server, it proves that it's certificate matches the summary. What this means technically is that it gives you a Merkle inclusion proof that goes back to the root.
Of course, actually deploying this in practice turns out to be a lot harder than it sounds, which I'll get to in the next post.