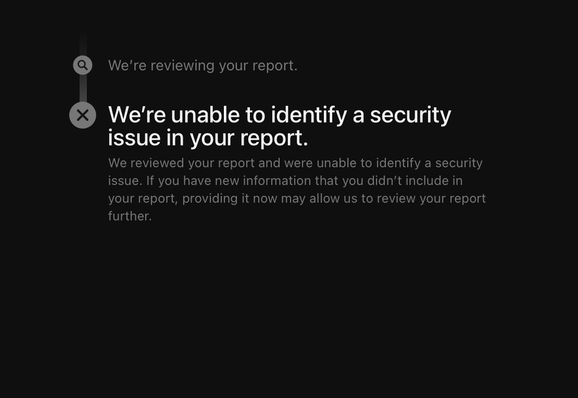
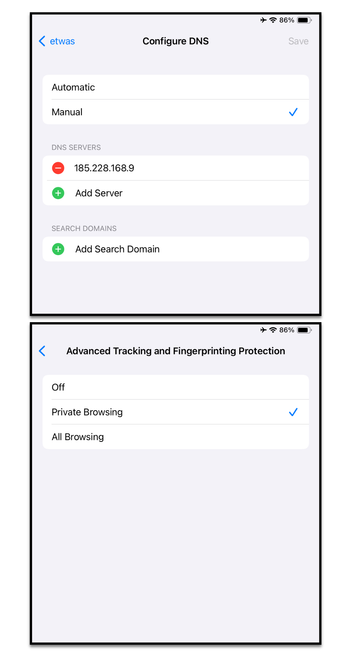
The "Advanced Tracking and Fingerprinting Protection" introduced in Safari in iOS 17 leaks DNS queries to Apple DNS server. Users who rely on custom DNS to block malware domains will be unprotected. We reported this bug to Apple, but Apple says it is not an issue.
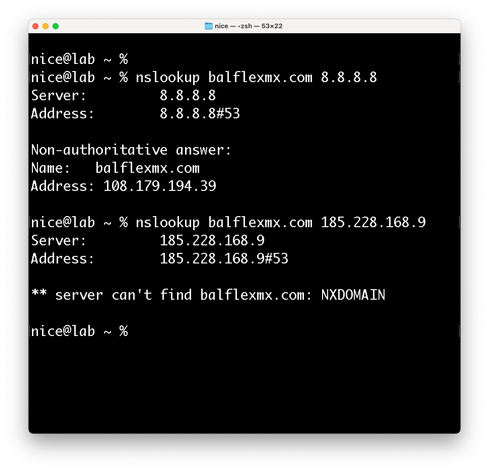
In our example, we configured the internet connection to use a DNS server from cleanbrowsing[.]org that blocks malware domains. With Advanced Tracking and Fingerprinting Protection enabled, we opened a website that should be blocked by the DNS server. Surprisingly, the page loaded. The nslookup command verifies that the custom DNS server does not resolve the domain name of this malware website. Network traffic shows that Apple's DoH DNS server resolved the website instead. In fact, only websites blocked by the custom DNS server are resolved by Apple's DNS.
🧵(1/2)
#privacy #security #cybersecurity #infosec #cybersecuritytips #iOS #macOS #Apple