@simonbs This seems like a really minor component of the not-quite-spam-but-almost I have to deal with.
Possibly because if I have the opportunity to use a better MFA system like FIDO or open TOTP I do that instead.
But I suppose a company that's implemented their own proprietary MFA system instead of using one of the widely deployed and reliable open ones wouldn't understand that.
@simonbs Yes. That's the point. You shouldn't have many of those. If you get enough that this seems like a worthwhile feature, you have a security problem.
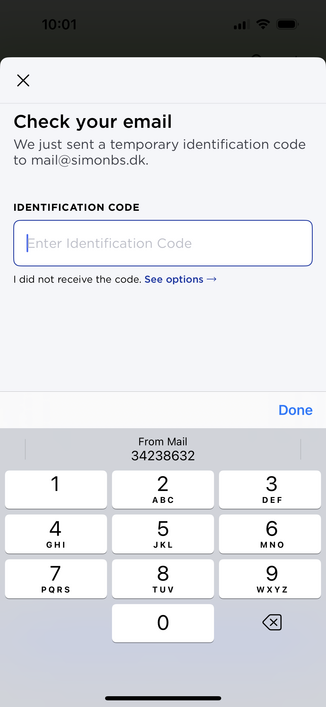
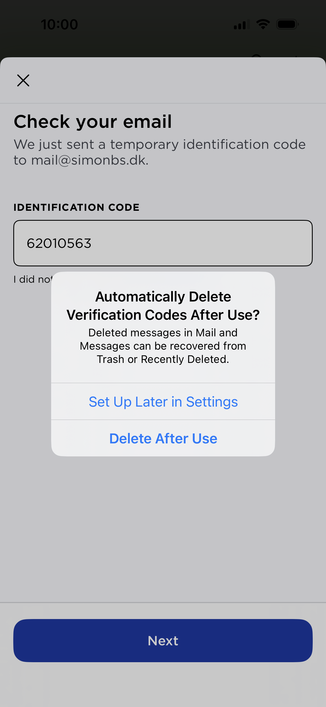
Verification codes through SMS or mail, except for the special case of verifying an email address during initial account setup, are so bad a security system that it's not clear they're not actually worse than not doing MFA at all. If you're routinely getting these that's a problem that needs to be fixed, not swept under the carpet.
@simonbs I have been using basically passkeys for ssh authentication for decades and it's great but it requires a lot more coordination on both ends. Getting desktop or ops to re-install my .ssh directory after an upgrade is a regular chore.
And of course given their choice to make their MFA solution proprietary and require buying an Apple mobile device I am sure their passkey solution will be open and well coordinated with third parties and competitors.
That's sarcasm by the way.