FOSDEM 2019: How to write a reverse proxy with Go in 25 minutes.
GitHub - yschaeff/ICantBelieveItsNotDNS: "I Can't Believe It's Not DNS!" (ICBIND) is an authoritative DNS server for the ESP8266 written in MicroPython.
"I Can't Believe It's Not DNS!" (ICBIND) is an authoritative DNS server for the ESP8266 written in MicroPython. - GitHub - yschaeff/ICantBelieveItsNotDNS: "I Can't Beli...
@b0rk Woah! This gives me a bit of an idea -- I've been implementing my own Layer 1 and Layer 2 in Go for fun/learning. It's very unstable and still has gremlins I'm working on purging, BUT:
I can exchange IP (including, via BGP, to the regular internet!). Only hiccup is it's ham bands, so I can't encrypt -- I wonder if there's a carve-out band for using my SDR at low power where I could import subtls on top of my Layer 1 / 2, and have an understandable stack from Layer 1 to TLS 🤯
@paul yes!!
I really want to get working layer 1 + layer 2 implementations that I can run over the normal internet on a Mac so that I can have the full stack, but I cannot figure out how to make tun/tap work on a Mac to save my life
(I already have ipv4 + tcp + udp + dns + tls implemented in Python)
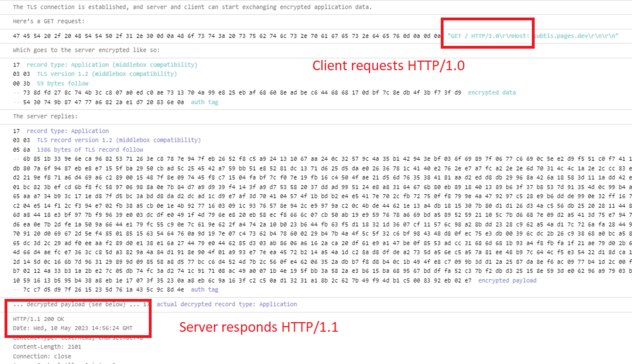
weird how server responds HTTP/1.1 for a 1.0 request 🤔