New blog post: "Abuse and Detection of Microsoft 365 Defender Live Response for privilege escalation on Control Plane (Tier0) assets"
Description of potential attack paths to gain privilege access to #ActiveDirectory and #AzureAD by abusing script execution and how to detect and mitigate them.
https://www.cloud-architekt.net/abuse-detection-live-response-tier0/
Abuse and Detection of M365D Live Response for privilege escalation on Control Plane (Tier0) assets
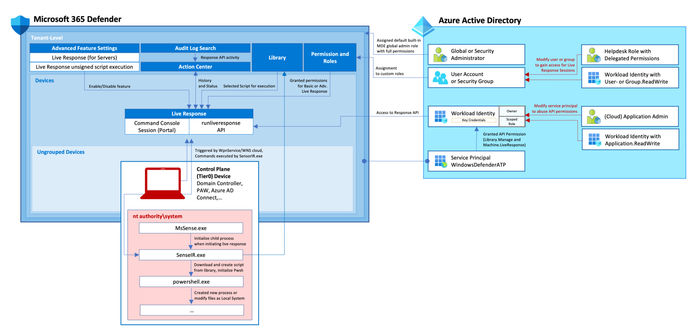
Live Response in Microsoft 365 Defender can be used to execute PowerShell scripts on protected devices for advanced incident investigation. But it can be also abused by Security Administrators for privilege escalation, such as creating (Active Directory) Domain Admin account or “phishing” access token from (Azure AD) Global Admin on a PAW device. In this blog post, I will describe the potential attack paths and a few approaches for detection but also mitigation.