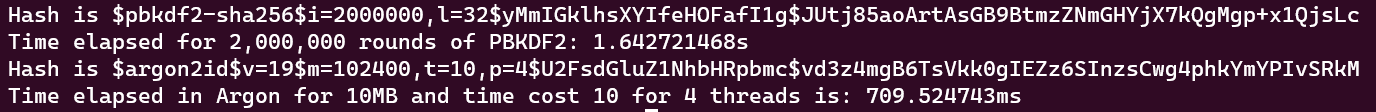
I wrote a piece of code in rust to test Argon2id vs PBDKF2 on a Dell D6400 being used as a Linux Ubuntu Server. The image are the speed tests. It seems that you can not set the time cost >10 in @bitwarden . I also read that you can't have the memory be larger than 120MB if you have an iPhone and use the fill process. I found that the delay on my iPhone 11 is <3 seconds when vault timeout occurs. I bet allocating 100MB takes a while on a phone : ) Using the timing on my machine, if the speedup for PBDKF2 is more than about twice as fast as Argon2id, you are more secure.
@MITREsteve @bitwarden I wonder how far can you push the PBDKF
@babyfangs @bitwarden I think in the rust application the number of rounds is a u32 so 4.2B I’ll have to look up the code tomorrow to see the limit on Bitwarden
@babyfangs @bitwarden
In mobile clients the rounds are a nuint which is a signed 32 or 64 bit int. If 32 bit then 2.1M. If 64 bits then 9,2 * 1018. Seeing that 2M took about a second, the max 64 bit number of rounds would take about a billion years to create one hash.
In mobile clients the rounds are a nuint which is a signed 32 or 64 bit int. If 32 bit then 2.1M. If 64 bits then 9,2 * 1018. Seeing that 2M took about a second, the max 64 bit number of rounds would take about a billion years to create one hash.
@MITREsteve @bitwarden I mean like would they allow that? As thats a sure fire way to get tickets from customers saying their vault is gone.