We at @SophosXOps have been tracking the growth of #malware threat actors taking advantage of a (previously) rarely abused Office file format - the .one files used by the #OneNote application. Now a more prominent malware group, Qakbot, has joined the fray. 1/6
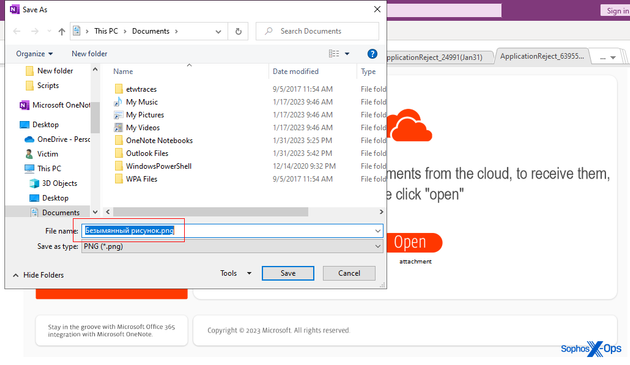
@SophosXOps Our initial look at this threat vector revealed #Qakbot has begun using the new technique in their #malspam campaigns, in a much more automated, streamlined fashion. The malicious OneNote "notebook" is a single page document that looks like this.
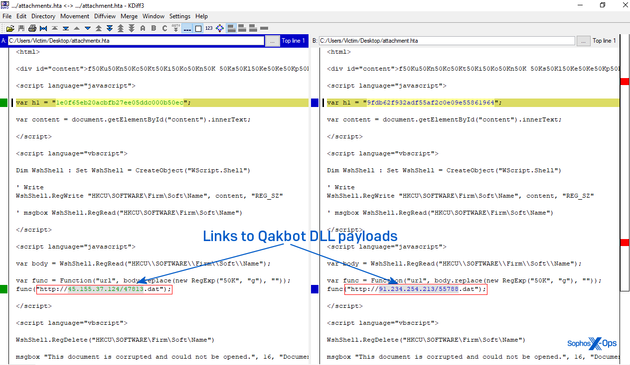
You can hover your mouse pointer over the "open" button on this document and see the way they linked to an embedded .hta in the notebook.
2/6
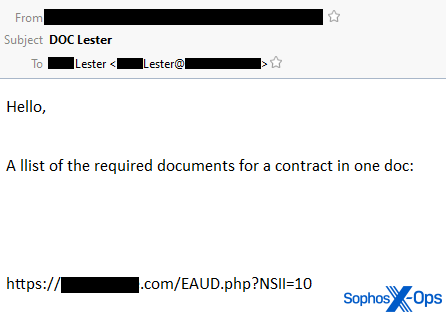
@SophosXOps #Qakbot's threat actors typically use email messages as their initial attack vector, "injecting" a malicious email into the middle of existing conversational threads, replying to all parties with either a #maldoc attachment or a link to a #malware file.
They're the worst kind of "reply guy" 3/6
@SophosXOps This is not exactly new behavior. In fact, a year ago I published an analysis into #Qakbot doing precisely the same thing (https://news.sophos.com/en-us/2022/03/10/qakbot-decoded/), but using a different infection vector.
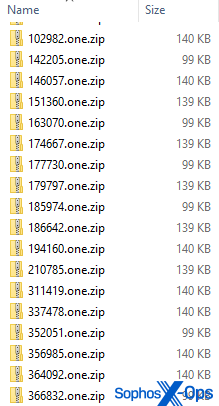
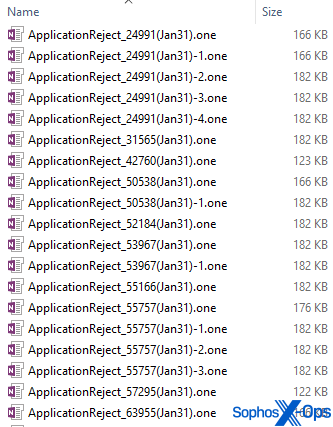
#Qakbot began using #malspam #OneNote .one Notebooks on January 31. We observed two #malspam forms: In one, the emails embed a link, prompting the recipient to download a weaponized .one file. In the other, they "reply guy" a OneNote attachment right into the thread.
4/6
@SophosXOps All the #OneNote #maldoc documents in this case contain a static image that prompts the user to click a button in response to text that says "This document contains attachments from the cloud, to receive them, double click 'open.'"
When you open the document, it spawns an embedded HTML Application (eg., an .hta file) with an embedded, obfuscated script in the DIV tag. That script retrieves a Qakbot DLL payload from a website and executes the initial infection command. 5/6
@SophosXOps
Our coverage of this #malware campaign includes a breakdown of the attack chain, IOCs, and some other curious details -- such as the fact that the embedded graphic elements were originally added to the document using filenames in the Russian language. "Curious," that.
People unfamiliar with OneNote as a weaponized document format should get used to this; #QakNote #maldocs are probably here to stay -- at least, until mail server admins decide to block all inbound .one attachments. 6/6
@SophosXOps My colleagues Colin Cowie (@th3_protoCOL), Benjamin Sollman (@bencrypted), and Stephen Ormandy were instrumental in bringing this to my attention and doing some of the legwork finding the attack vectors.
We've published IOCs to our Github, here (expect periodic updates at this link): https://github.com/sophoslabs/IoCs/blob/master/Qakbot-onenote-attacks.csv