Ported my @covidsewage bot over to Mastodon
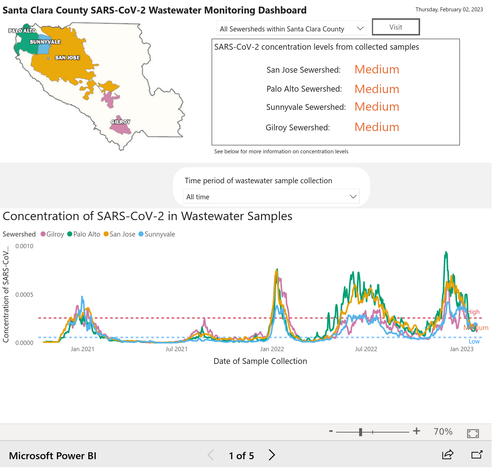
Every morning it posts an image with the latest Covid sewage charts for various locations around the San Francisco Bay Area - because the sewage charts are the only figures I still trust!
The sewage doesn't lie
The screenshots come from https://covid19.sccgov.org/dashboard-wastewater - here's the latest image: