#Metasploit Framework 6.3 is out now 🎉
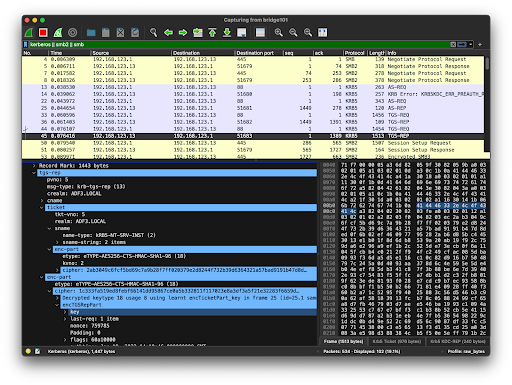
New features include native #Kerberos authentication support, streamlined Active Directory attack workflows (AD CS, AD DS), and new modules that request, forge, and convert tickets between formats.
https://www.rapid7.com/blog/post/2023/01/30/metasploit-framework-6-3-released/