While
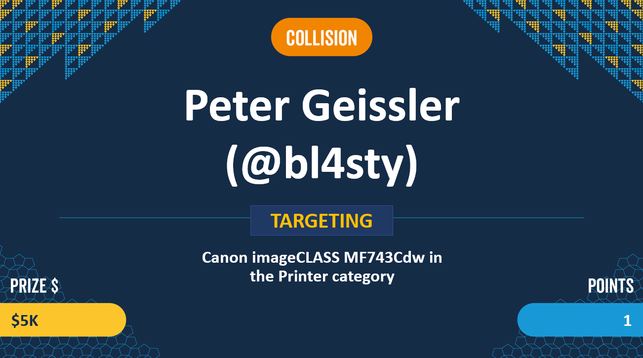
@bl4sty
only scored a COLLISION (non-unique bug) - Peter definitely gets a boatload of STYLE POINTS for this hack on a Canon printer @ #P2OToronto #Pwn2Own
@bl4sty
only scored a COLLISION (non-unique bug) - Peter definitely gets a boatload of STYLE POINTS for this hack on a Canon printer @ #P2OToronto #Pwn2Own