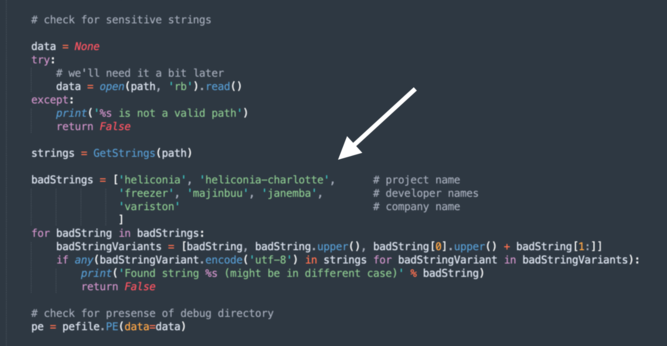
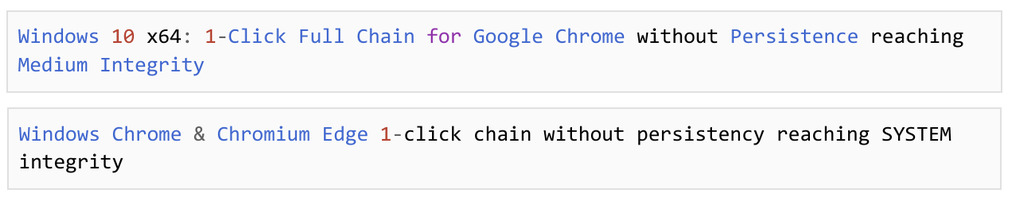
New: Google says Variston IT, a Barcelona-based spyware vendor, is behind an exploitation framework that exploited zero-day flaws in Chrome, Firefox and Windows Defender as far back as 2018.
My colleague @carlypage has more: https://techcrunch.com/2022/11/30/variston-spyware-chrome-firefox-windows/