On Nov 21st #ESETResearch detected and alerted @_CERT_UA of a wave of ransomware we named #RansomBoggs, deployed in multiple organizations in Ukraine🇺🇦. While the malware written in .NET is new, its deployment is similar to previous attacks attributed to #Sandworm. 1/9
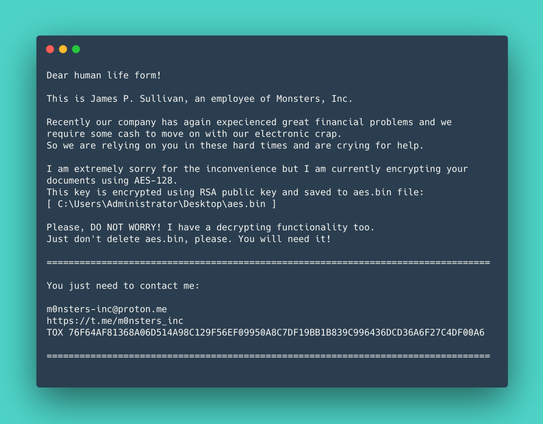
Its authors make multiple references to Monsters, Inc., the 2001 movie by Pixar. The ransom note (SullivanDecryptsYourFiles.txt) shows the authors impersonate James P. Sullivan, the main character of the movie, whose job is to scare kids. 2/9
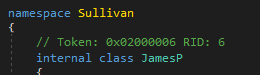
The executable file is also named Sullivan.<version?>.exe and references are present in the code as well. 3/9
There are similarities with previous attacks conducted by #Sandworm: a PowerShell script used to distribute the .NET ransomware from the domain controller is almost identical to the one seen last April during the #Industroyer2 attacks against the energy sector. 4/9
This PowerShell script is what @_CERT_UA calls #POWERGAP, and was used to deploy #CaddyWiper using #ArguePatch (see https://cert.gov.ua/article/39518). 5/9
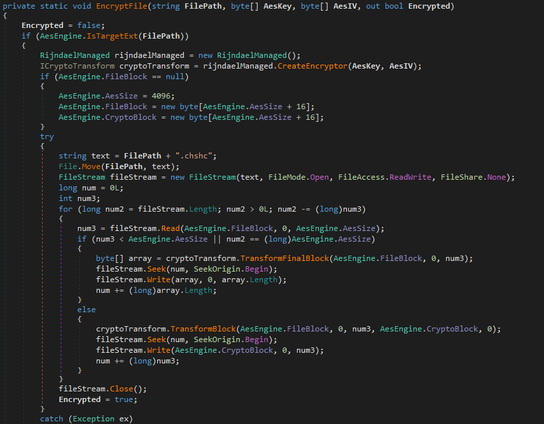
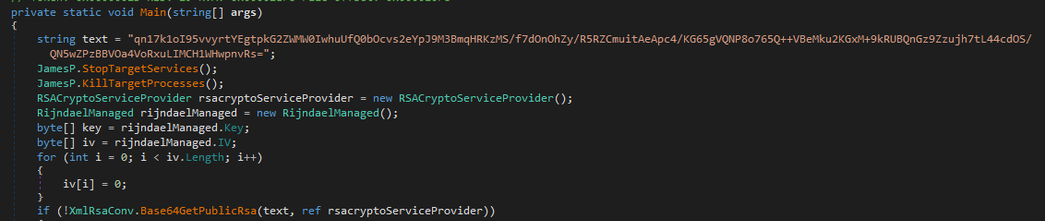
RansomBoggs generates a random key and encrypts files using AES-256 in CBC mode (not AES-128 like mentioned in the ransom note), and appends the .chsch file extension. The key is then RSA encrypted and written to aes.bin. 6/9
Depending on the malware variant, the RSA public key can either be hardcoded in the malware sample itself or provided as argument. 7/9
Last month, Microsoft notified about a similar operation in Ukraine and Poland, where ransomware called #Prestige hit logistics companies. They also attributed these attacks to #Sandworm. 8/9
https://twitter.com/MsftSecIntel/status/1580998124721823745
https://twitter.com/MsftSecIntel/status/1580998124721823745
Microsoft Security Intelligence on Twitter
“Microsoft has identified a new ransomware strain "Prestige" in limited targeted attacks in Ukraine and Poland. Several notable features differentiate this ransomware from other campaigns and payloads tracked by MSTIC. Get TTPs and protection info: https://t.co/4E3gaj1K7b”
IoCs:
F4D1C047923B9D10031BB709AABF1A250AB0AAA2
021308C361C8DE7C38EF135BC3B53439EB4DA0B4
ESET Detection names:
MSIL/Filecoder.Sullivan.A
MSIL/Filecoder.RansomBoggs.A
9/9
F4D1C047923B9D10031BB709AABF1A250AB0AAA2
021308C361C8DE7C38EF135BC3B53439EB4DA0B4
ESET Detection names:
MSIL/Filecoder.Sullivan.A
MSIL/Filecoder.RansomBoggs.A
9/9
@ESETresearch Are you able to share the SHA256 hashes for these files?
@ColinGrady @ESETresearch
78dcf144e82e947c20f152a8a57376b43e7aac3fee4bf1d18d22d4c14b25e56f
a490d03e780a6b664da65e20afa7845c6f79af60b6a496ff113bf9e9034e77d0
78dcf144e82e947c20f152a8a57376b43e7aac3fee4bf1d18d22d4c14b25e56f
a490d03e780a6b664da65e20afa7845c6f79af60b6a496ff113bf9e9034e77d0
@nyx__o @ESETresearch Thank you!