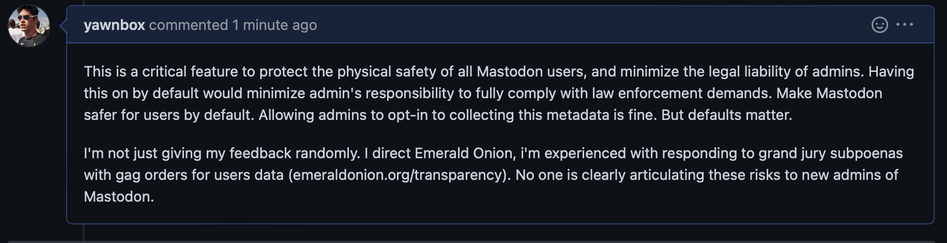
because direct messages on Mastodon are clear-text, all admins are subject to warrants from their local/regional law enforcement agencies
same with usage metadata like IP addresses and time stamps
i disabled IP logging in UFW and nginx, but Mastodon itself still logs this to be able to present it to the user for authentication transparency
making mastodon more resistant to targeted surveillance would be valuable to protect users