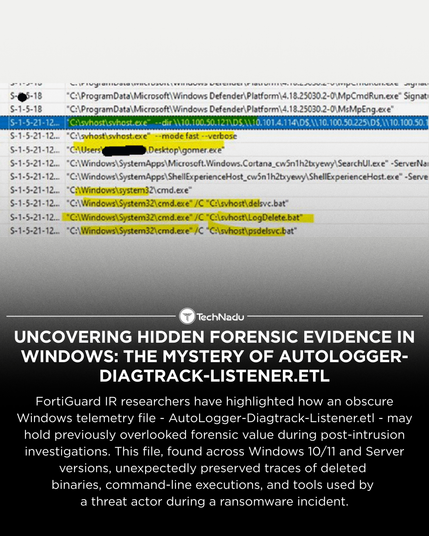
FortiGuard IR researchers have highlighted unexpected forensic value in the AutoLogger-Diagtrack-Listener.etl file on modern Windows systems.
Despite low exploitation severity, the artefact has shown the ability to preserve historical process-execution data, including deleted binaries and command-line traces — helpful in ransomware investigations.
What’s your view on ETW-based artefacts in DFIR workflows?
Share your insights and follow us for more clear, unbiased analysis.
#InfoSec #DFIR #ThreatIntel #WindowsForensics #ETW #Telemetry #CyberSecurity #IncidentResponse #SecurityResearch #ThreatAnalysis