Sebastian Roth on Twitter
“Ever wondered if all clients get the same level of security? In our newest @USENIXSecurity paper, we discovered that sometimes the configuration of security headers depends on client characteristics. Read it here: https://t.co/tDIFqJP5O7 CC: @stecalzavara @kcotsneb @CISPA”
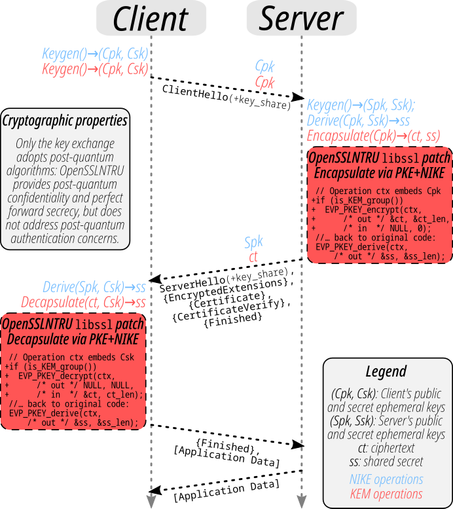
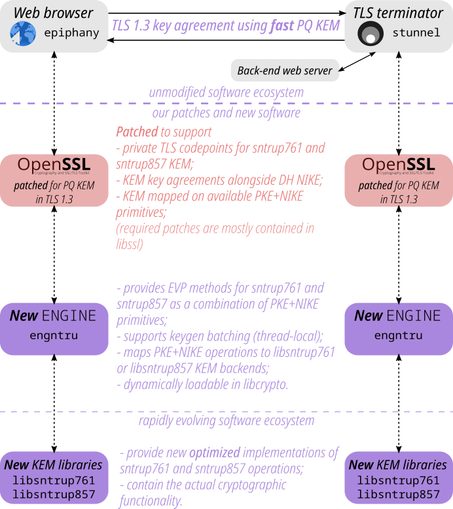
 Visit opensslntru.cr.yp.to for updated demo, FOSS artifacts, & preprint!
Visit opensslntru.cr.yp.to for updated demo, FOSS artifacts, & preprint!